
In this tutorial, we are going to learn how to install and configure Nessus scanner on Ubuntu 18.04/CentOS 7 server. Identifying vulnerabilities is the first step towards securing your environment. Nessus is the de-facto industry standard vulnerability assessment solution. It helps to easily identify and fix vulnerabilities – including software flaws, missing patches, malware, and misconfigurations across a variety of operating systems, devices and applications.
Note that Nessus is a commercial solution and in this tutorial, we are going to use a free trial version.
Table of Contents
Installing Nessus Scanner on Ubuntu/CentOS
Download and Install Nessus
Nessus installation package can be downloaded from here. Once the download completes, run the installation as follows.
On Ubuntu 18.04
dpkg -i Nessus-7.2.1-ubuntu1110_amd64.debIf the installation is successful, you should see an output shown below;
...output snipped...
Unpacking Nessus Scanner Core Components...
- You can start Nessus Scanner by typing /etc/init.d/nessusd start
- Then go to https://<your-hostname>:8834/ to configure your scanner
...snipped...For CentOS 7
yum localinstall Nessus-7.2.1-es7.x86_64.rpm...output snipped...
Installing : Nessus-7.2.1-es7.x86_64 1/1
Unpacking Nessus Core Components...
- You can start Nessus by typing /bin/systemctl start nessusd.service
- Then go to https://<your-hostname>:8834/ to configure your scanner
...output snipped...Where <your-hostname> is the hostname of your machine.
Allow Nessus Web Access on Firewall
If firewall is running, you need to open Nessus port 8834 to access the web User Interface.
For Ubuntu and simillar derivatives
ufw allow 8834For CentOS and simillar derivatives;
firewall-cmd --add-port=8834/tcp --permanent
firewall-cmd --reloadStart Nessus Deamon
After the installation is complete, you can start Nessus deamon by running the command below as shown in the installation output.
/etc/init.d/nessusd startor you can simply use the command below.
systemctl start nessusdTo enable Nessus to start on system reboot, run the command below;
systemctl enable nessusdSet up and Activate Nessus
After initial installation you are required to set up and activate Nessus. Login to UI, using the link as shown in the installation output: https://<your-hostname>:8834/. When you enter that link, add the SSL error that displays as an exception and proceed.
Create Nessus Administrator Account
Next, you are required to create an admin account.
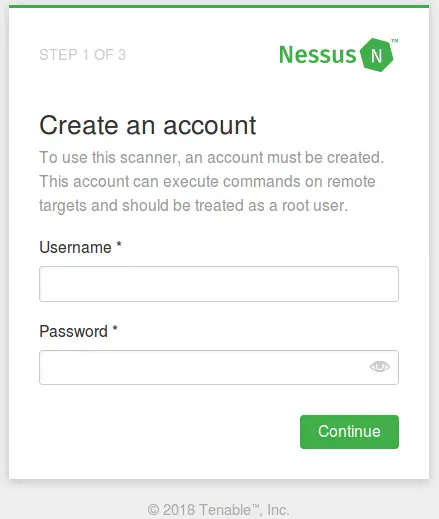
You may also create a new Nessus user from Nessus CLI using the command below;
/opt/nessus/sbin/nessuscli adduserRegister Nessus Scanner
Note that you need an activation code for you to register Nessus. To obtain the trail activation code, you need to register here if you have not done so.
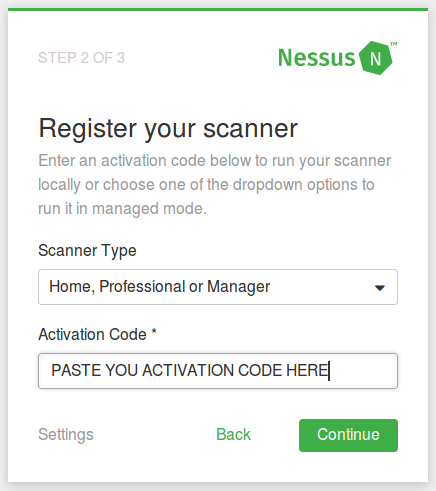
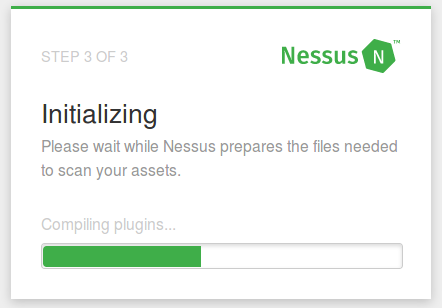
Choose the Scanner Type and enter the activation code. Once the Nessus setup is complete, it will start to initialize by downloading and compiling the plugins needed for scanning. This may take a while though.
Nessus Pro Dashboard
Once initialization is complete, the Nessus dashboard is launched that looks like the one below;
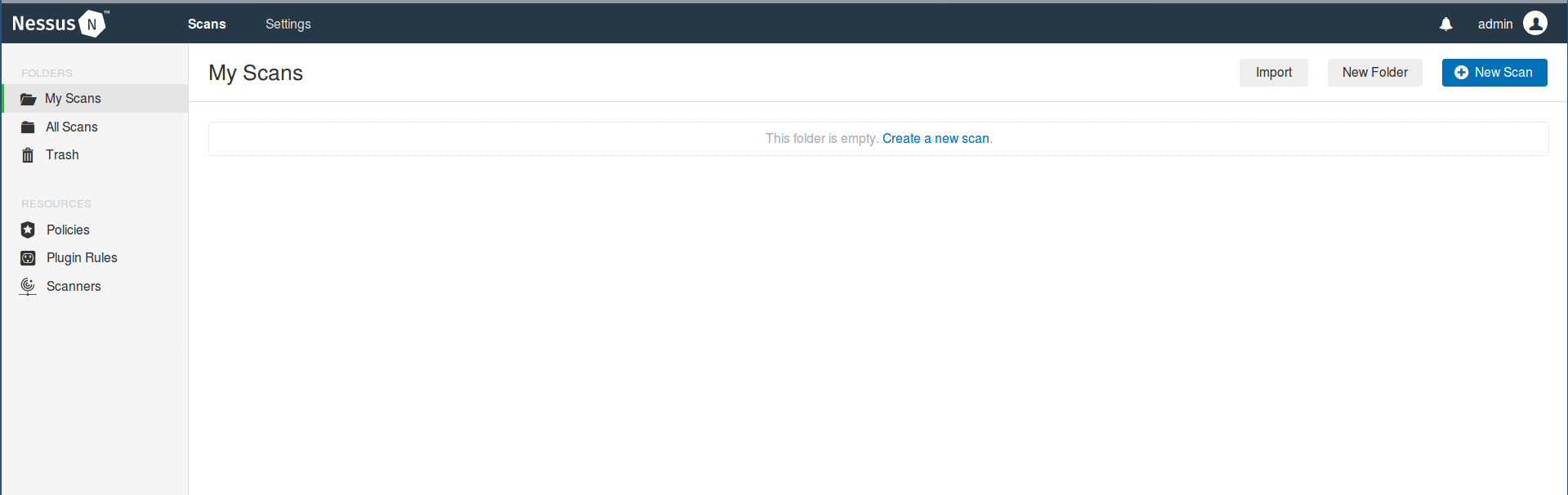
The installation and setup is now complete and you can now embark on hunting vulnerabilities in your systems.
Learn how to scan assets/hosts using Nessus by following the link below;
How to Scan a Remote Host using Nessus Vulnerability Scanner
Other Related Tutorials
How to Install and Use Nikto Web Scanner on Ubuntu 18.04
How to Install RKHunter (RootKit Hunter) On Ubuntu 18.04

