Is it possible to configure Apache Tomcat to run over HTTPS? Yes, this guide provides a step by step tutorial on how to configure Apache Tomcat with HTTPS. Apache Tomcat (or simply Tomcat) is an open source web server and servlet container developed by the Apache Software Foundation (ASF). Tomcat implements the Java Servlet and the JavaServer Pages (JSP) specifications from Oracle, and provides a “pure Java” HTTP web server environment for Java code to run in.
Table of Contents
Configuring Apache Tomcat with HTTPS
Why HTTPS for Apache Tomcat?
Using HTTPS for Apache Tomcat is recommended for several important reasons:
- Security: HTTPS provides encryption and data integrity, ensuring that the data exchanged between the client (user’s web browser) and the Tomcat server remains confidential. Without HTTPS, data can be intercepted or tampered with during transmission, putting sensitive information at risk.
- Credentials Protection: Apache Tomcat often requires users to enter credentials (e.g., usernames, passwords) to access manager app or host manager. With HTTPS, these credentials are encrypted and protected from potential eavesdropping.
- e.t.c
Install and Setup Apache Tomcat
Of course you need to have Apache Tomcat server up and running.
You can check our guides on how to install and setup Apache Tomcat.
Generating Apache Tomcat SSL/TLS Certificates
Which SSL/TLS Certificates are Supported by Apache Tomcat
Being Java-based, Apache Tomcat primarily supports two certificate formats for SSL/TLS configuration:Java Keystore (JKS) format and PEM format.
- Java Keystore (JKS) Format: Java Keystore is the native format used by Java applications, including Apache Tomcat. It’s a binary format that can store various types of cryptographic information, including private keys, certificates, and certificate chains. Tomcat’s native SSL connector supports JKS as the keystore format.
- PEM Format: Although not a native format, Apache Tomcat also supports PEM-encoded certificates and private keys. Tomcat can work with PEM-encoded files through the OpenSSL library and its APR (Apache Portable Runtime) connector. This allows you to use certificates and keys in PEM format directly with Tomcat.
As a result, you can have your SSL/TLS certificates in JKS or PEM formats.
NOTE: We are using Self-Signed SSL Certificates in this guide for the purposes of the demo. If your server is public facing, ensure that you use SSL/TLS certificates from trusted CAs.
Generating SSL/TLS Certificates in PEM Format
Generate CA Private Key
Run the following OpenSSL command to generate a private key for your CA:
mkdir /opt/tomcat9/sslopenssl genpkey -algorithm RSA -out /opt/tomcat9/ssl/ca.keyThe command generates an RSA private key and saves it in the file /opt/tomcat9/ssl/ca.key.
Generate CA self-signed certificate
Once you have the private key, you can now generate the CA self-signed certificate using the command below. When the command runs, you are prompted to provide information about your CA, such as the common name, organization, and location, contact email e.t.c. Common Name, must be provided.
openssl req -x509 -new -key /opt/tomcat9/ssl/ca.key -days 3650 -out /opt/tomcat9/ssl/ca.crtSample output;
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:US
State or Province Name (full name) [Some-State]:California
Locality Name (eg, city) []:San Francisco
Organization Name (eg, company) [Internet Widgits Pty Ltd]:Kifarunix-Demo Inc
Organizational Unit Name (eg, section) []:Infrastracture
Common Name (e.g. server FQDN or YOUR name) []:tomcat.kifarunix-demo.com
Email Address []:
You can provide all these information from the command line using the -subj option.
openssl req -x509 -new \
-key /opt/tomcat9/ssl/ca.key \
-days 3560 \
-out /opt/tomcat9/ssl/ca.crt \
-subj "/C=US/ST=California/L=San Francisco/O=Kifarunix-Demo Inc/CN=tomcat.kifarunix-demo.com/[email protected]"
Note that it is not recommended to use wildcard CN. Instead, use SAN to define your other domains/IPs/wildcards.
Generate Server Private Key and CSR
Next, generate the server private key and certificate signing request (CSR).
openssl req -new \
-newkey rsa:4096 \
-nodes \
-keyout /opt/tomcat9/ssl/server.key \
-out /opt/tomcat9/ssl/server.csr \
-subj "/C=US/ST=California/L=San Francisco/O=Kifarunix-Demo Inc/CN=tomcat.kifarunix-demo.com/[email protected]"
Generate and Sign Server Certificate
Now, you need to generate the server certificate using the CSR, the CA cert and private key.
Note that since OpenSSL command doesn’t include the extensions such as Subject Alternative Names on the certificate, you need to provide this information manually.
SAN extension allows you to include additional subject names, such as domain names or IP addresses, in a single certificate, thus allowing a certificate to be valid for multiple entities or alternative names.
So, create a CNF file with your SAN extensions;
vim /opt/tomcat9/ssl/san.cnfauthorityKeyIdentifier=keyid,issuer
basicConstraints=CA:FALSE
keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment
subjectAltName = @alt_names
[alt_names]
DNS.1=kifarunix-demo.com
DNS.2=*.kifarunix-demo.com
then generate and sign the server certificate;
openssl x509 -req \
-in /opt/tomcat9/ssl/server.csr \
-CA /opt/tomcat9/ssl/ca.crt \
-CAkey /opt/tomcat9/ssl/ca.key \
-CAcreateserial \
-out /opt/tomcat9/ssl/server.crt \
-days 3650 \
-extfile /opt/tomcat9/ssl/san.cnf
Sample output;
Certificate request self-signature ok
subject=C = US, ST = California, L = San Francisco, O = Kifarunix-Demo Inc, CN = tomcat.kifarunix-demo.com, emailAddress = [email protected]So you now have the server, CA certificate and key under /opt/tomcat9/ssl/ in PEM format.
Ensure Tomcat user has ownership of the SSL/TLS certificate files;
chown -R tomcat: /opt/tomcat9/ssl/Generating SSL/TLS Certificates in JKS Format
You can also generate the certificate files in JKS format.
If you already have the certificate files in PEM format as above, then you can convert them JKS as follows.
Convert the ;
openssl pkcs12 -export \
-in /opt/tomcat9/ssl/server.crt \
-inkey /opt/tomcat9/ssl/server.key \
-name tomcat \
-out /opt/tomcat9/ssl/tomcat.p12
Provide the keystore password and keep that password somewhere you can easily retrieve.
Create Java KeyStore (JKS), import the server and CA certificates:
Set the keystore password. When prompted, trust the certificate.
keytool -importcert \
-file /opt/tomcat9/ssl/ca.crt \
-alias kifarunix-demo-CA \
-keystore /opt/tomcat9/ssl/keystore.jks
Next, import the server certificate to keystore. Provide both source and destination keystore password.
keytool -importkeystore \
-srckeystore /opt/tomcat9/ssl/tomcat.p12 \
-srcstoretype pkcs12 \
-destkeystore /opt/tomcat9/ssl/keystore.jks \
-deststoretype JKS
To confirm the keystore details;
keytool -list -v -keystore /opt/tomcat9/ssl/keystore.jksIf you do not have any PEM files already, then simply execute the command below to generate JKS;
keytool -genkey \
-alias tomcat \
-keyalg RSA \
-validity 3650 \
-keystore /opt/tomcat9/ssl/tomcat.jks
sample output;
Enter keystore password:
Re-enter new password:
What is your first and last name?
[Unknown]: Kifarunix Demo
What is the name of your organizational unit?
[Unknown]: Infrastructure
What is the name of your organization?
[Unknown]: Kifarunix-demo Inc
What is the name of your City or Locality?
[Unknown]: San Francisco
What is the name of your State or Province?
[Unknown]: California
What is the two-letter country code for this unit?
[Unknown]: US
Is CN=Kifarunix Demo, OU=Infrastructure, O=Kifarunix-demo Inc, L=San Francisco, ST=California, C=US correct?
[no]: yes
Generating 2,048 bit RSA key pair and self-signed certificate (SHA256withRSA) with a validity of 3650 days
for: CN=Kifarunix Demo, OU=Infrastructure, O=Kifarunix-demo Inc, L=San Francisco, ST=California, C=US
Similarly, ensure Tomcat user has ownership of the SSL/TLS certificate files;
chown -R tomcat: /opt/tomcat9/ssl/Enable Apache Tomcat HTTPS Using PEM SSL/TLS Certificate files
If you are using PEM SSL/TLS certificate files, this is how you can enable HTTPs on Apache Tomcat.
Please note that
Tomcat can use three different implementations of SSL:
- JSSE implementation provided as part of the Java runtime
- JSSE implementation that uses OpenSSL
- APR implementation, which uses the OpenSSL engine by default
For Tomcat to automatically choose its proper SSL implementation, you can configure the Connector with generic protocol="HTTP/1.1". Read more on SSL/TLS configuration page.
Thus, edit the conf/server.xml file in the Tomcat installation directory.
vim /opt/tomcat9/conf/server.xmlAdd the following configuration under the <Service>… </service> section;
<Connector port="8443" protocol="HTTP/1.1"
maxThreads="150" SSLEnabled="true" scheme="https" secure="true"
maxParameterCount="1000"
>
<UpgradeProtocol className="org.apache.coyote.http2.Http2Protocol" />
<SSLHostConfig>
<Certificate certificateKeyFile="/opt/tomcat9/ssl/server.key"
certificateFile="/opt/tomcat9/ssl/server.crt"
certificateChainFile="/opt/tomcat9/ssl/ca.crt"
type="RSA" />
</SSLHostConfig>
</Connector>
Replace paths to SSL/TLS certificates accordingly.
Save and exit when done.
Restart Apache Tomcat to apply the changes;
systemctl restart tomcat9Check if Apache Tomcat HTTPS, 8443/TCP, port is opened now;
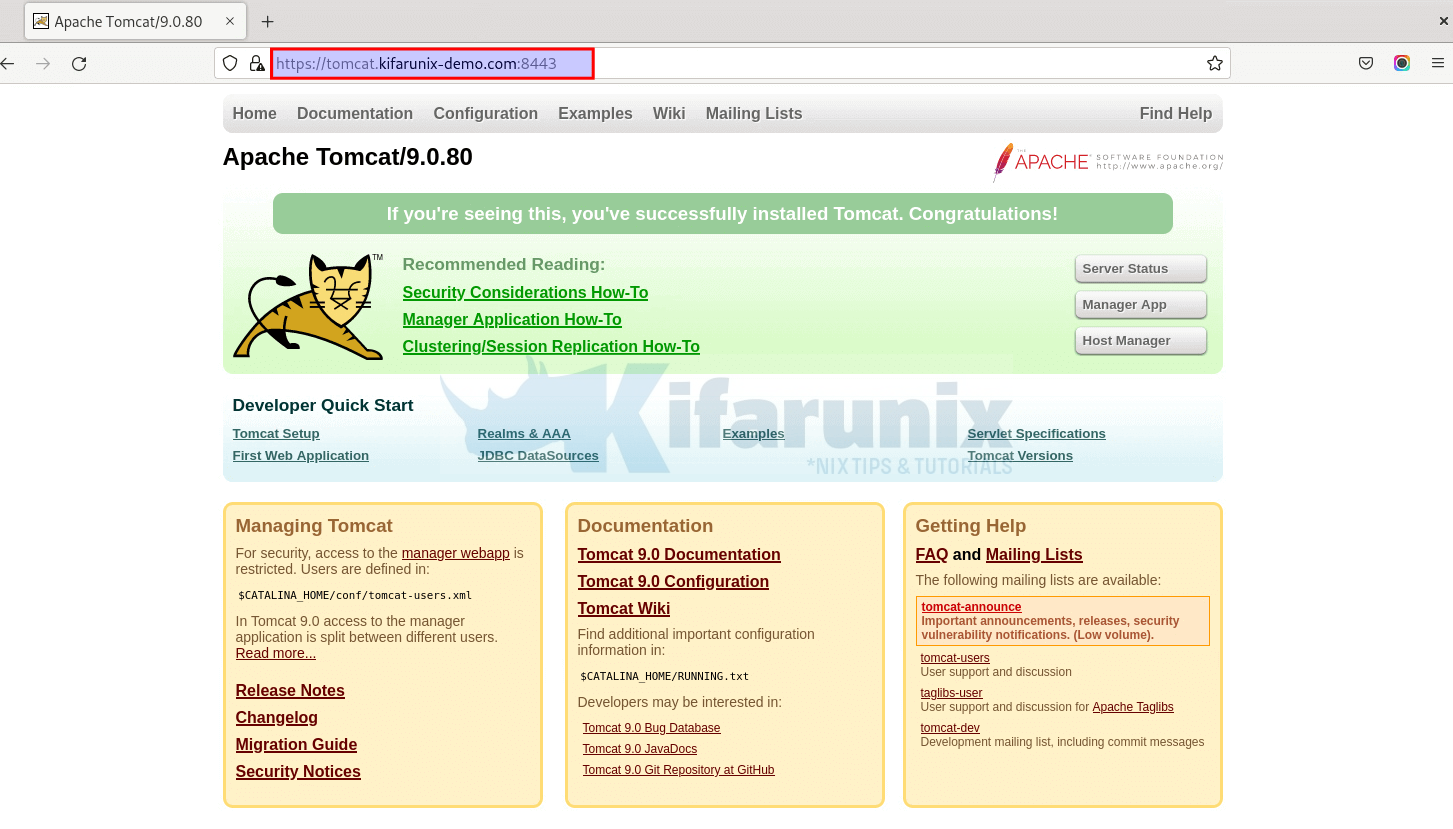
ss -altnp | grep :8443LISTEN 0 100 *:8443 *:* users:(("java",pid=27651,fd=45))You should now be able to access your websever via HTTPS on port 8443, https://tomcat.kifarunix-demo.com:8443.
Enable Apache Tomcat HTTPS Using JKS SSL/TLS Certificate files
If you are using SSL/TLS files in JKS format, update Apache Tomcat server.xml file as follows;
vim /opt/tomcat9/conf/server.xml <Connector port="8443" protocol="HTTP/1.1"
maxThreads="150" SSLEnabled="true" scheme="https" secure="true"
maxParameterCount="1000"
keystoreFile="/opt/tomcat9/ssl/keystore.jks"
>
<UpgradeProtocol className="org.apache.coyote.http2.Http2Protocol" />
</Connector>
If you set keystore password, then you need to define it with the correct password!
<Connector port="8443" protocol="HTTP/1.1"
maxThreads="150" SSLEnabled="true" scheme="https" secure="true"
maxParameterCount="1000"
keystoreFile="/opt/tomcat9/ssl/keystore.jks"
keystorePass="ChangeME"
>
<UpgradeProtocol className="org.apache.coyote.http2.Http2Protocol" />
</Connector>
If you are setting your keystore password here in the file, ensure access to this system is restricted and monitored.
Save and exit the files.
Accessing Apache Tomcat via HTTPS
Now that Apache Tomcat is configured with HTTPS, you can now access it via HTTPS, https://tomcat.kifarunix-demo.com:8443/tomcat.
Redirecting Apache Tomcat HTTP to HTTPS
By now, our Apache Tomcat is listening on both HTTP and HTTPS;
ss -altnp | grep javaLISTEN 0 100 *:8080 *:* users:(("java",pid=28087,fd=43))
LISTEN 0 1 [::ffff:127.0.0.1]:8005 *:* users:(("java",pid=28087,fd=54))
LISTEN 0 100 *:8443 *:* users:(("java",pid=28087,fd=45))
So, how can you configure Apache Tomcat to redirect HTTP to HTTPS? Apache Tomcat can be configured to redirect HTTP to HTTPS using the rewrite valve which implements URL rewrite functionality in a way that is very similar to mod_rewrite from Apache HTTP Server.
The rewrite valve is configured as a valve using the org.apache.catalina.valves.rewrite.RewriteValve class name (<Valve className="org.apache.catalina.valves.rewrite.RewriteValve" />)
Thus, edit the Apache Tomcat context.xml file and add the valve class name as follows;
vim /opt/tomcat9/conf/context.xml<?xml version="1.0" encoding="UTF-8"?>
<!--
Licensed to the Apache Software Foundation (ASF) under one or more
contributor license agreements. See the NOTICE file distributed with
this work for additional information regarding copyright ownership.
The ASF licenses this file to You under the Apache License, Version 2.0
(the "License"); you may not use this file except in compliance with
the License. You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software
distributed under the License is distributed on an "AS IS" BASIS,
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
See the License for the specific language governing permissions and
limitations under the License.
-->
<!-- The contents of this file will be loaded for each web application -->
<Context>
<!-- Default set of monitored resources. If one of these changes, the -->
<!-- web application will be reloaded. -->
<WatchedResource>WEB-INF/web.xml</WatchedResource>
<WatchedResource>WEB-INF/tomcat-web.xml</WatchedResource>
<WatchedResource>${catalina.base}/conf/web.xml</WatchedResource>
<!-- Uncomment this to disable session persistence across Tomcat restarts -->
<!--
<Manager pathname="" />
-->
<Valve className="org.apache.catalina.valves.rewrite.RewriteValve" />
</Context>
Save and exit the file.
Next, create a rewrite.config file under the WEB-INF directory of the web application with your HTTP to HTTPS rewrite directives;
vim /opt/tomcat9/webapps/ROOT/WEB-INF/rewrite.configRewriteCond %{SERVER_PORT} ^8080$
RewriteRule ^(.*)$ https://%{HTTP_HOST}:8443$1 [R=301,L]
This will redirect anything accessed on port 8080 to port 8443. Play around with these directives to suite your requirements.
Save and exit the file.
Next, ensure redirect is enabled on the server.xml file.
<Connector port="8080" protocol="HTTP/1.1"
connectionTimeout="20000"
redirectPort="8443"
maxParameterCount="1000"
/>
Save and exit the file.
Restart Apache Tomcat;
systemctl restart tomcat9Verify Apache Tomcat HTTP to HTTPS redirection.

