In this tutorial, you will learn how to enable basic authentication on ELK stack. Elastic/ELK stack supports user authentication. This enables it to restrict access to various resources within the cluster. To access these resources when authentication is enabled, a user has to prove their identity using username/passwords or other forms of identity depending on the authentication realm enabled.
Note that this guide is tested only on a single node cluster.
Table of Contents
Enabling Authentication on ELK Stack
Apart from the usual basic username and password authentication, Elastic stack supports other authentication services such as LDAP, Active Directory etc.
Before you can proceed, ensure you have a running Elastic stack;
Install ELK Stack on Debian 11
Install ELK Stack on Rocky Linux 8
Thus, to enable basic authentication on ELK stack;
Stop both Kibana and Elasticsearch
To stop Kibana service, run the command below. Note that we assume that you are using a system that uses SystemD to control service unit.
systemctl stop kibanaDepending on whether you are running a single node or a cluster of Elasticsearch nodes, run the command below to stop the service.
systemctl stop elasticsearchEnable Elasticsearch Security Features
If you are running ELK stack with a basic or trial License, the basic security is disabled by default. Thus, to enable basic security feature in Elasticsearch, set the value of xpack.security.enabled to true in Elasticsearch configuration file, ES_PATH_CONF/elasticsearch.yml. Where ES_PATH_CONF can be /etc/elasticsearch as for my setup.
Thus, this can be done by running the command below;
sed -i.bak '$ a xpack.security.enabled: true' /etc/elasticsearch/elasticsearch.ymlThe command will create a back up file for the configuration file and appends the line, xpack.security.enabled: true at the end of the file.
Start Elasticsearch
systemctl start elasticsearchCreate Passwords for In-built Elastic Users
When basic security features are enabled, basic authentication is automatically enabled. Hence, as such, without valid username/password for authentication, you wont access Elastic stack.
Elastic ships with some in-built users such as elastic, which is a superuser, kibana_system which is used to connect Kibana and Elasticsearch e.t.c. Read more on Elastic Built-in users page.
Elasticsearch user password can be generates using the command /usr/share/elasticsearch/bin/elasticsearch-setup-passwords.
There are two ways in which you can create passwords for Inbuilt Elastic users;
- Generate passwords interactively
- Generate passwords automatically
Generate passwords interactively
This method allows you to set the passwords you want for various Elastic built-in users.
To generate the passwords interactively, run the command below;
/usr/share/elasticsearch/bin/elasticsearch-setup-passwords interactiveYou will then be prompted to enter the passwords for various users, elastic,apm_system,kibana,kibana_system,logstash_system,beats_system,remote_monitoring_user.
Generate passwords automatically
You can generate the password automatically using the command below;
echo "y" | /usr/share/elasticsearch/bin/elasticsearch-setup-passwords autoSample output;
Initiating the setup of passwords for reserved users elastic,apm_system,kibana,kibana_system,logstash_system,beats_system,remote_monitoring_user.
The passwords will be randomly generated and printed to the console.
Changed password for user apm_system
PASSWORD apm_system = OWBOmkrSKjejSIEVRCz4
Changed password for user kibana_system
PASSWORD kibana_system = zX4p4dRZMSLuJvGAU8JM
Changed password for user kibana
PASSWORD kibana = zX4p4dRZMSLuJvGAU8JM
Changed password for user logstash_system
PASSWORD logstash_system = ttObhClVaUkY738GA9CH
Changed password for user beats_system
PASSWORD beats_system = II5dlBzMw3q5fH7FqM47
Changed password for user remote_monitoring_user
PASSWORD remote_monitoring_user = JSUaYVewkHrzucK7tUfK
Changed password for user elastic
PASSWORD elastic = MxT3fuPCbxhwdQ3sQKNZ
Note, Be sure to save all these passwords as they are needed to be used later.
Enable Kibana-Elasticsearch Authenticated connection
When Elastic security features are enabled, Kibana has to connect to Elasticsearch using valid credentials.
The credentials we gonna use in our setup are:
Changed password for user kibana_system
PASSWORD kibana_system = zX4p4dRZMSLuJvGAU8JMSet the authentication username
By default, the username to use is kibana_system. Thus, you need to define the username by uncommenting the line, #elasticsearch.username: "kibana_system" by running the command below;
sed -i.bak '/\.username/s/^#//' /etc/kibana/kibana.ymlDefine the username password. Ensure you use the password generated above. You can securely store the password in Kibana instead of setting it in plain text in the kibana.yml configuration file using the command;
/usr/share/kibana/bin/kibana-keystore create/usr/share/kibana/bin/kibana-keystore add elasticsearch.passwordWhen prompted, enter the password for kibana_system user, which is zX4p4dRZMSLuJvGAU8JM.
Enter value for elasticsearch.password: ********************Start Kibana Service
You can now start Kibana service;
systemctl start kibanaKibana Login Page
When you now access your Kibana web interface, you will be prompted to enter the login credentials to access the web UI.
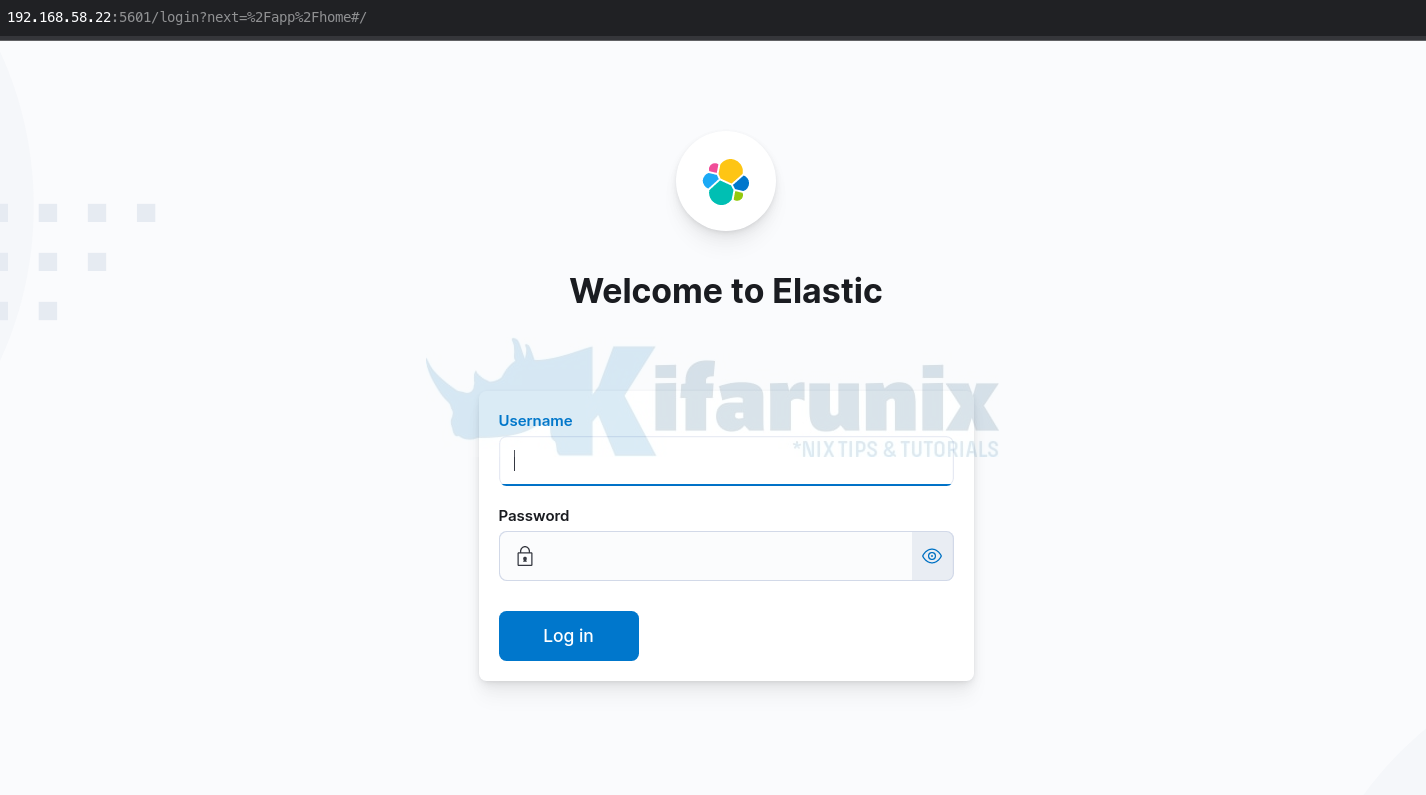
For now, you can login using the superuser account, elastic and its password generated above.
Note that you can also add other file based users using the elasticsearch-users command.
For example, to add another admin user, run the command below;
/usr/share/elasticsearch/bin/elasticsearch-users useradd kifarunix -r superuserSome of the known roles include;
kibana_dashboard_only_user, apm_system, watcher_admin, viewer, logstash_system, rollup_user, kibana_user, beats_admin, remote_monitoring_agent, rollup_admin, data_frame_transforms_admin, snapshot_user, monitoring_user, enrich_user, kibana_admin, logstash_admin, editor, machine_learning_user, data_frame_transforms_user, machine_learning_admin, watcher_user, apm_user, beats_system, reporting_user, transform_user, kibana_system, transform_admin, transport_client, remote_monitoring_collector, superuser, ingest_adminRead more about elasticsearch-users command on Elastic page.
You can also add other users and their roles on Kibana Management > Stack Management > Security > [Users, Roles].
And that is how you can enable basic authentication on ELK Stack. In our next tutorial, you will learn how to enable Filebeat – Elasticsearch authentication so as to be able to write events to the Elasticsearch indices.
Reference
Other Tutorials
Enable HTTPS Connection Between Elasticsearch Nodes

