In this guide, you will learn how to install Wireshark on Rocky Linux. Wireshark is the world’s foremost and widely-used network protocol analyzer.
Some of the features of Wireshark include;
- Deep inspection of hundreds of protocols, with more being added all the time
- Live capture and offline analysis
- Standard three-pane packet browser
- Multi-platform: Runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others
- Captured network data can be browsed via a GUI, or via the TTY-mode TShark utility
- The most powerful display filters in the industry
- Rich VoIP analysis
- Read/write many different capture file formats: tcpdump (libpcap), Pcap NG, Catapult DCT2000, Cisco Secure IDS iplog, Microsoft Network Monitor …
- Capture files compressed with gzip can be decompressed on the fly
- Live data can be read from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others (depending on your platform)
- Decryption support for many protocols, including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Coloring rules can be applied to the packet list for quick, intuitive analysis
- Output can be exported to XML, PostScript, CSV, or plain text
Note that it is a criminal act to scan or sniff on any network traffic without any clearance to do so, otherwise using it may land you in jail.
Install Wireshark on Rocky Linux
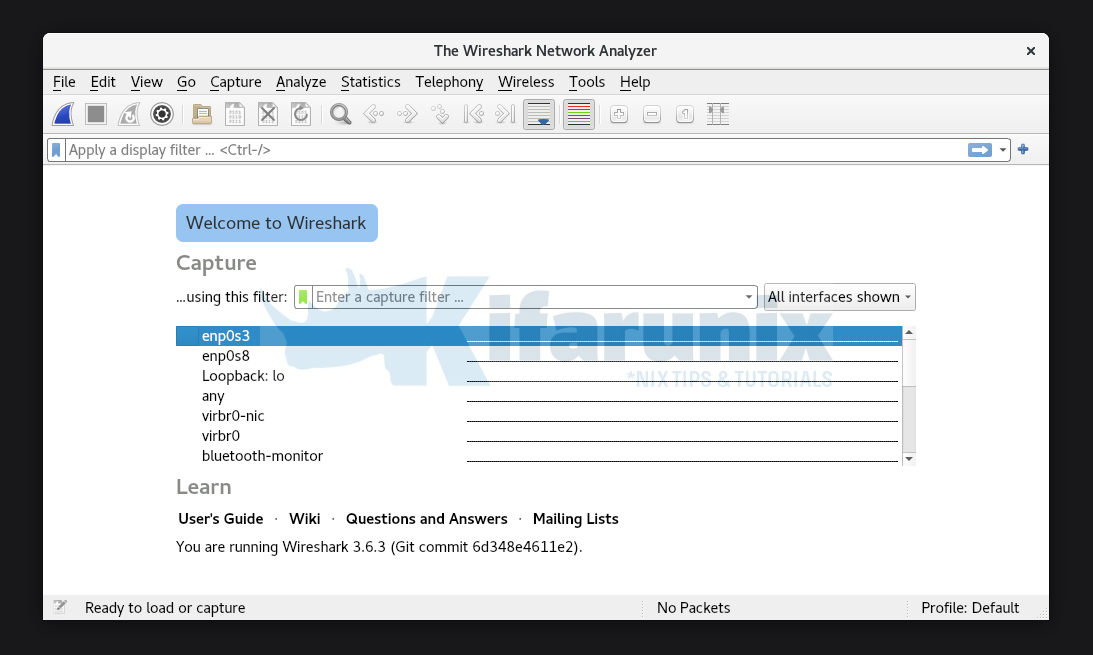
Wireshark is available on the default Rocky Linux repositories. However, the available versions may not be the up-to-date. Wireshark 3.6.3 is the current stable release as of this writing.
Well, to confirm this, run the commands below to check the available version of Wireshark on Rocky Linux;
sudo dnf info wiresharkCommand output;
Available Packages
Name : wireshark
Epoch : 1
Version : 2.6.2
Release : 14.el8
Architecture : x86_64
Size : 3.6 M
Source : wireshark-2.6.2-14.el8.src.rpm
Repository : appstream
Summary : Network traffic analyzer
URL : http://www.wireshark.org/
License : GPL+
As you can see, the latest version of Wireshark is available on Rocky Linux.
Hence, to install the latest release version of Wireshark on Rocky Linux, you need to build it from the source.
To build Wireshark from the source on Rocky Linux;
Install Required Build tools
dnf install qt5-devel gcc gcc-c++ bison flex libpcap-devel \
gtk3-devel rpm-build libtool c-ares-devel qt5-qtbase-devel \
qt5-qtmultimedia-devel qt5-linguist desktop-file-utils \
createrepo glib2-devel perl perl-devel tcpdump libcap-devel \
libssh-devel krb5-devel perl-Parse-Yapp snappy-devel git\
minizip-devel lz4 libxml2-devel spandsp-devel systemd-devel -yCompile and Install Wireshark
Download Wireshark latest source code from downloads page.
wget https://1.eu.dl.wireshark.org/src/wireshark-3.6.3.tar.xzExtract the Wireshark source code.
tar xJf wireshark-3.6.3.tar.xzCompile Wireshark source code
cd wireshark-3.6.3cmake .Sample command output;
...
-- The following OPTIONAL packages have been found:
* Git
* GMODULE2
* Gettext
* LIBSSH (required version >= 0.6), Library for implementing SSH clients,
Support for profiles import/export
* SNAPPY, A fast compressor/decompressor from Google,
Support for G.722 and G.726 codecs in RTP player
* LibXml2
* CAP, The Libcap package implements the user-space interfaces to the POSIX 1003.1e capabilities available in Linux kernels,
Support for GeoIP lookup
* SMI, Library to access SMI management information,
LZ4 decompression in CQL and Kafka dissectors, read compressed capture files
* ZSTD (required version >= 1.0.0), A compressor/decompressor from Facebook providing better compression than Snappy at a cost of speed,
Header decompression in HTTP2
* LUA (required version >= 5.1)
* NL, Libraries for using the Netlink protocol on Linux,
Support for playing SBC codec in RTP player
* BCG729, G.729 decoder,
Support for G.729 codec in RTP player
* ILBC, iLBC decoder,
Support for iLBC codec in RTP player
* OPUS, opus decoder, Fix any errors before you proceed, just in case there is any.
Build Wireshark
makeInstall Wireshark
make installRunning Wireshark on Rocky Linux
You can now launch Wireshark either from command line or from the activities;
Wireshark interface;
Tshark command line utility is also installed;
tshark --help
TShark (Wireshark) 3.6.3 (Git commit 6d348e4611e2)
Dump and analyze network traffic.
See https://www.wireshark.org for more information.
Usage: tshark [options] ...
Capture interface:
-i , --interface
name or idx of interface (def: first non-loopback)
-f packet filter in libpcap filter syntax
-s , --snapshot-length
packet snapshot length (def: appropriate maximum)
-p, --no-promiscuous-mode
don't capture in promiscuous mode
-I, --monitor-mode capture in monitor mode, if available
-B , --buffer-size
size of kernel buffer (def: 2MB)
-y , --linktype
link layer type (def: first appropriate)
--time-stamp-type timestamp method for interface
-D, --list-interfaces print list of interfaces and exit
-L, --list-data-link-types
print list of link-layer types of iface and exit
--list-time-stamp-types print list of timestamp types for iface and exit
Capture stop conditions:
-c stop after n packets (def: infinite)
-a ..., --autostop ...
duration:NUM - stop after NUM seconds
filesize:NUM - stop this file after NUM KB
files:NUM - stop after NUM files
packets:NUM - stop after NUM packets
Capture output:
-b ..., --ring-buffer
duration:NUM - switch to next file after NUM secs
filesize:NUM - switch to next file after NUM KB
files:NUM - ringbuffer: replace after NUM files
packets:NUM - switch to next file after NUM packets
interval:NUM - switch to next file when the time is
an exact multiple of NUM secs
Input file:
-r , --read-file
set the filename to read from (or '-' for stdin)
Processing:
-2 perform a two-pass analysis
-M perform session auto reset
-R , --read-filter
packet Read filter in Wireshark display filter syntax
(requires -2)
-Y , --display-filter
packet displaY filter in Wireshark display filter
syntax
-n disable all name resolutions (def: "mNd" enabled, or
as set in preferences)
-N enable specific name resolution(s): "mnNtdv"
-d ==, ...
"Decode As", see the man page for details
Example: tcp.port==8888,http
-H read a list of entries from a hosts file, which will
then be written to a capture file. (Implies -W n)
--enable-protocol
enable dissection of proto_name
--disable-protocol
disable dissection of proto_name
--enable-heuristic
enable dissection of heuristic protocol
--disable-heuristic
disable dissection of heuristic protocol
Output:
-w write packets to a pcapng-format file named "outfile"
(or '-' for stdout)
--capture-comment
add a capture file comment, if supported
-C start with specified configuration profile
-F And there you go. Wireshark is now running on Rocky Linux.
Other Tutorials