Well, assuming you understand the implications of the expired SSL/TLS certificates, let us go through how to monitor SSL/TLS Certificates Expiry with Nagios. Nagios provides SSL Certificate monitoring and alerting when SSL certificates expiration date draws closer using the Nagios Plugins.
Before you can proceed, install and setup Nagios server. Follow the links below to setup Nagios server on your desired system.
Install Nagios Server on CentOS 8
Install Nagios Core on Debian 10 Buster
Monitoring SSL/TLS Certificates Expiry with Nagios
Once your Nagios server is up and ready proceed to configure it to monitor your web servers SSL/TLS certificates expiry.
check_http Nagios plugin is used to test the HTTP service on the specified host. It can test normal (http) and secure (https) servers, follow redirects, search for strings and regular expressions, check connection times, and report on certificate expiration times.
Reporting on certificate expiration times is the main focus of this guide.
Install Nagios Plugins
Nagios plugins provide the check_http plugin script. Below is a sample guide on how to install Nagios plugins on the Nagios server.
Install Nagios Plugins From Source RHEL/CentOS/Oracle Linux
Add the Host to Nagios Server
Next, you need to add the host whose SSL/TLS certificates is to be monitored to Nagios Server. See a sample guide below;
Add Hosts to Nagios Server For Monitoring
Create Check_HTTP Command Object Definition
Create a command object definition that defines how to use the check_http command to monitor the SSL/TLS certificates.
If you compiled Nagios from the source, then create the command definition configuration on /usr/local/nagios/etc/objects. You can also use your own custom sub-directory, like /usr/local/nagios/etc/objects/kifarunix-demo, for our case.
Be sure to replace PATHS accordingly.
vim /usr/local/nagios/etc/objects/kifarunix-demo/commands.cfg# Check SSL/TLS Certificate Expiry Command Definition
define command{
command_name check_certs
command_line /usr/local/nagios/libexec/check_http -S -I $HOSTADDRESS$ -p $ARG1$ -C $ARG2$
}- The command is named
check_certsand will be called in the service definition using this name. /usr/local/nagios/libexec/check_httpspecifies the location of the Nagios script.-Sinstructs the check_http plugin to check the SSL port which defaults to 443.-Ioption specifies IP address or name of the host. You can as well use the-Hoption for hostname argument for servers using host headers (virtual host).-pspecifies port number to check. Useful if you want to check SSL for other ports ike SMTPS, IMAPS, POP3S-Cspecifies the minimum number of days a certificate has to be valid.
Create Check_HTTP Service Object Definition
After creating the command object definition to check SSL certificate, proceed to define a service that calls the check_certs object defined above.
vim /usr/local/nagios/etc/objects/kifarunix-demo/services.cfgdefine service{
use kifarunix-demo-service
host_name web01.kifarunix-demo.com
service_description HTTPS SSL Certificate
check_command check_certs!443!10
}- The
usestatement defines the service template to use. host_namespecifies the host to check the SSL expiry against.service_descriptionis the description of the service name.check_commandspecifies the name of the command that should be used to check SSL certificate as defined on the command definition above.- 443 is the SSL port to check. The value for the
-p $ARG1$. !10specifies the value of the-C $ARG2$in the command definition. Hence, you will receive notification 10 days to certificate expiry.
If you need to monitor other ports like SMTPS, POPS, IMAPS, you can add such service definitions to your Service Object definition configuration file.
define service{
use kifarunix-demo-service
host_name mail.kifarunix-demo.com
service_description SMTP SSL Certificate
check_command check_certs!465!10
}
define service{
use kifarunix-demo-service
host_name mail.kifarunix-demo.com
service_description SMTP TLS Certificate
check_command check_certs!587!10
}
define service{
use kifarunix-demo-service
host_name mail.kifarunix-demo.com
service_description IMAPS Certificate
check_command check_certs!993!10
}
define service{
use kifarunix-demo-service
host_name mail.kifarunix-demo.com
service_description POP3 SSL Certificate
check_command check_certs!995!10
}Verify Nagios Configuration
It is a wise idea to check Nagios configuration of syntax errors everytime you make changes.
/usr/local/nagios/bin/nagios -v /usr/local/nagios/etc/nagios.cfg...
Total Warnings: 0
Total Errors: 0
Things look okay - No serious problems were detected during the pre-flight checkIf there are no errors, restart Nagios service.
systemctl restart nagiosVerify the SSL checks from command line;
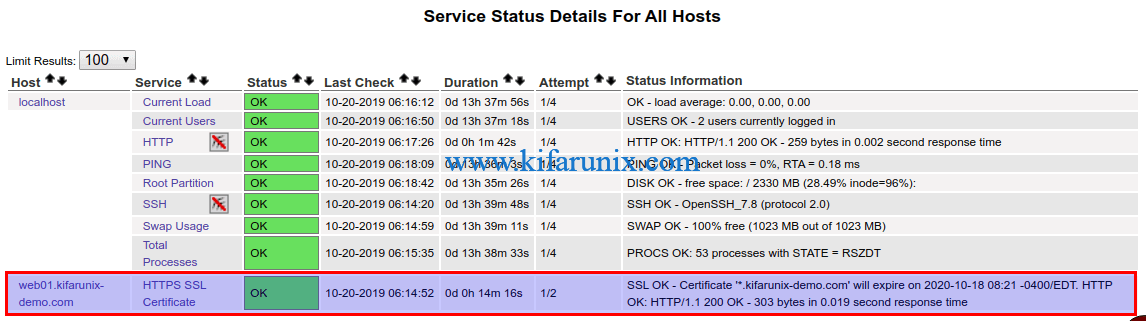
/usr/local/nagios/libexec/check_http -I web01.kifarunix-demo.com -p 443 -C 10SSL OK - Certificate '*.kifarunix-demo.com' will expire on 2020-10-18 08:21 -0400/EDT. HTTP OK: HTTP/1.1 200 OK - 303 bytes in 0.025 second response time |time=0.025159s;;;0.000000 size=303B;;;0/usr/local/nagios/libexec/check_http -I mail.kifarunix-demo.com -p 465 -C 20SSL WARNING - Certificate 'mx01.kifarunix-demo.com' expires in 12 day(s) (2019-11-08 23:14 +0000/EDT).You can also Navigate to Nagios web interface to verify the SSL checks.
There you go. You will now be notified when you SSL/TLS certificate expiry date is 10 days or below.
Want to be notified via Email? Follow the link below to learn how to configure Nagios email notification using Gmail.
Configure Nagios Email Notification Using Gmail
See other Nagios guides by following the links below;

