In this guide, you will learn how to install GVM 21.04 on Debian 11/Debian 10. Greenbone Vulnerability Management (GVM), previously known as OpenVAS, is a network security scanner which provides a set of network vulnerability tests (NVTs) to detect security loopholes in systems and applications. As of this writing, GVM 21.04 is the current stable release.
Want to use Rocky Linux 8 instead?
Install GVM 21.04 on Rocky Linux 8
Table of Contents
Installing GVM on Debian
Prerequisites
In this demo, we will install and setup GVM 21.04 on Debian 11/Debian 10 from source code. As such, below are the system requirements I would personally recommend.
- At least 4 GB RAM
- At least 4 vCPUs
- More than 8 GB disk space (We used 16 GB in this demo)
These requirements will vary depending on your use cases, however. Just be sure to provide “enough”.
Run System Update
To begin with, update and upgrade your system packages;
apt updateapt upgradeCreate GVM User on Ubuntu
In this demo, we will run GVM 21.08 as a non privileged system user. Thus, create gvm system user account.
useradd -r -d /opt/gvm -c "GVM User" -s /bin/bash gvmCreate the GVM user directory as specified by option -d in the command above and set the user and group ownership to gvm.
mkdir /opt/gvm && chown gvm: /opt/gvmInstall Required Build Tools
In order to successfully build GVM 21.04 on Debian 11/Debian 10, you need to install a number of required dependencies and build tools.
apt install gcc g++ make bison flex libksba-dev \
curl redis libpcap-dev cmake git pkg-config libglib2.0-dev libgpgme-dev \
nmap libgnutls28-dev uuid-dev libssh-gcrypt-dev libldap2-dev gnutls-bin \
libmicrohttpd-dev libhiredis-dev zlib1g-dev libxml2-dev libnet-dev libradcli-dev \
clang-format libldap2-dev doxygen gcc-mingw-w64 xml-twig-tools libical-dev perl-base \
heimdal-dev libpopt-dev libunistring-dev graphviz libsnmp-dev python3-setuptools \
python3-paramiko python3-lxml python3-defusedxml python3-dev gettext python3-polib \
xmltoman python3-pip texlive-fonts-recommended \
texlive-latex-extra --no-install-recommends xsltproc sudo vim rsync -y
Install Yarn on Debian 11/Debian 10
Next, install Yarn JavaScript package manager
curl -sL https://dl.yarnpkg.com/debian/pubkey.gpg | gpg --dearmor | sudo tee /usr/share/keyrings/yarnkey.gpg >/dev/nullecho "deb [signed-by=/usr/share/keyrings/yarnkey.gpg] https://dl.yarnpkg.com/debian stable main" | sudo tee /etc/apt/sources.list.d/yarn.listapt updateapt install yarn -yInstall PostgreSQL on Debian 11/Debian 10
GVM 21.04 uses PostgreSQL as the backend database. We use version 11 in this setup.
On Debian 10, run the command below to install PostgreSQL;
apt install postgresql-11 postgresql-contrib-11 postgresql-server-dev-11 -yOn Debian 11, run the command below;
echo "deb http://apt.postgresql.org/pub/repos/apt $(lsb_release -cs)-pgdg main" > /etc/apt/sources.list.d/pgdg.list
curl -sL https://www.postgresql.org/media/keys/ACCC4CF8.asc | sudo tee /etc/apt/trusted.gpg.d/pgdg.asc >/dev/null
apt update
apt install postgresql-11 postgresql-contrib-11 postgresql-server-dev-11 -yCreate PostgreSQL User and Database
Once the installation is done, create the PostgreSQL user and database for Greenbone Vulnerability Management Daemon (gvmd).
Note that the database and user should be created as PostgreSQL user, postgres.
sudo -Hiu postgres
createuser gvm
createdb -O gvm gvmdGrant PostgreSQL User DBA Roles
psql gvmd
create role dba with superuser noinherit;
grant dba to gvm;
\q
exitOnce that is done, restart PostgreSQL;
systemctl restart postgresqlsystemctl enable postgresqlAllow the user to run the installation with sudo rights;
echo "gvm ALL = NOPASSWD: $(which make) install" > /etc/sudoers.d/gvmBuilding GVM 21.04 from Source Code
There are different tools required to install and setup GVM 21.04 on Debian 11/Debian 10. These include;
- GVM Libraries
- OpenVAS Scanner
- OSPd
- ospd-openvas
- Greenbone Vulnerability Manager
- Greenbone Security Assistant
- Python-GVM
- GVM-Tools
- OpenVAS SMB
Every component has README.md and a INSTALL.md file that explains how to build and install it.
Build and Install GVM
Switch to GVM user created above;
su - gvmCreate a directory where to download the source files to;
mkdir gvm-sourceDownload GVM 21.04 Source Files
Navigate to temporary directory created above and run the subsequent commands to clone the GVM github branch files.
cd gvm-sourcegit clone -b stable --single-branch https://github.com/greenbone/gvm-libs.gitgit clone -b main --single-branch https://github.com/greenbone/openvas-smb.gitgit clone -b stable --single-branch https://github.com/greenbone/openvas.gitgit clone -b stable --single-branch https://github.com/greenbone/ospd.gitgit clone -b stable --single-branch https://github.com/greenbone/ospd-openvas.gitgit clone -b stable --single-branch https://github.com/greenbone/gvmd.gitgit clone -b stable --single-branch https://github.com/greenbone/gsa.gitgit clone -b stable --single-branch https://github.com/greenbone/gsad.gitOnce the source files are in place, proceed to build and install GVM.
Note the current working directory;
pwd/opt/gvm/gvm-sourcels -1gsa
gvmd
gvm-libs
openvas
openvas-smb
ospd
openvas-smbI would suggest you take a snapshot of your machine at this point, just in case things don’t work out, you can revert to this stage without having to start from scratch!
Note that we will install all GVM 21.04 files and libraries to the default location, /usr/local.
Build and Install GVM 11 Libraries
whoamigvmFrom within the source directory, /opt/gvm/gvm-source, in this setup, change to GVM libraries directory;
cd gvm-libs
mkdir build && cd build
cmake ..
make
sudo make installBuild and Install OpenVAS scanner and OpenVAS SMB
Open Vulnerability Assessment Scanner (OpenVAS) is a full-featured scan engine that executes a continuously updated and extended feed of Network Vulnerability Tests (NVTs).
OpenVAS SMB provides modules for the OpenVAS Scanner to interface with Microsoft Windows Systems through the Windows Management Instrumentation API and a winexe binary to execute processes remotely on that system.
Build and install openvas-smb;
cd ../../openvas-smb/
mkdir build && cd build
cmake ..
make
sudo make installBuild and install OpenVAS scanner;
cd ../../openvas
[ -d build ] || mkdir build && cd build
cmake ..
make
sudo make installConfiguring OpenVAS Scanner
The host scan information is stored temporarily on Redis server.
To begin run the command below to create the cache to the installed shared libraries;
exitldconfigThe default configuration of Redis server is /etc/redis/redis.conf.
Next, copy OpenVAS scanner Redis configuration file from the OpenVAS source directory, redis-openvas.conf, to the Redis config directory;
cp /opt/gvm/gvm-source/openvas/config/redis-openvas.conf /etc/redis/Update the ownership of the configuration.
chown redis:redis /etc/redis/redis-openvas.confUpdate the path to Redis unix socket on the /etc/openvas/openvas.conf using the db_address parameter.
To get the path to the Redis unix socket, run the command;
grep unixsocket /etc/redis/redis-openvas.confSample output;
unixsocket /run/redis-openvas/redis.sock
unixsocketperm 770Once you get the path to Redis unix socket, run the command;
echo "db_address = /run/redis-openvas/redis.sock" > /etc/openvas/openvas.confAdd gvm user to redis group;
usermod -aG redis gvmOptimize Redis Performance
You can also optimize Redis server itself improve the performance by making the following adjustments;
Increase the value of somaxconn in order to avoid slow clients connections issues.
echo "net.core.somaxconn = 1024" >> /etc/sysctl.confRedis background save may fail under low memory condition. To avoid this, enable memory overcommit (man 5 proc).
echo 'vm.overcommit_memory = 1' >> /etc/sysctl.confReload sysctl variables created above.
sysctl -pTo avoid creation of latencies and memory usage issues with Redis, disable Linux Kernel’s support for Transparent Huge Pages (THP). To easily work around this, create a systemd service unit for this purpose.
cat > /etc/systemd/system/disable_thp.service << 'EOL'
[Unit]
Description=Disable Kernel Support for Transparent Huge Pages (THP)
[Service]
Type=simple
ExecStart=/bin/sh -c "echo 'never' > /sys/kernel/mm/transparent_hugepage/enabled && echo 'never' > /sys/kernel/mm/transparent_hugepage/defrag"
[Install]
WantedBy=multi-user.target
EOL
Reload systemd configurations;
systemctl daemon-reloadStart and enable this service to run on system boot.
systemctl enable --now disable_thpRestart OpenVAS Redis server
systemctl enable --now redis-server@openvasConfirm the status;
systemctl status redis-server@openvas● [email protected] - Advanced key-value store (openvas)
Loaded: loaded (/lib/systemd/system/[email protected]; enabled; vendor preset: enabled)
Active: active (running) since Sat 2021-08-28 09:40:06 EAT; 5s ago
Docs: http://redis.io/documentation,
man:redis-server(1)
Main PID: 9001 (redis-server)
Status: "Ready to accept connections"
Tasks: 5 (limit: 4679)
Memory: 2.9M
CPU: 42ms
CGroup: /system.slice/system-redis\x2dserver.slice/[email protected]
└─9001 /usr/bin/redis-server 127.0.0.1:0
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis-server[9001]: `-._ `-._`-.__.-'_.-' _.-'
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis-server[9001]: `-._ `-.__.-' _.-'
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis-server[9001]: `-._ _.-'
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis-server[9001]: `-.__.-'
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis[9001]: _._
_.-``__ ''-._
_.-`` `. `_. ''-._ Redis 6.0.15 (00000000/0) 64 bit
.-`` .-```. ```\/ _.,_ ''-._
( ' , .-` | `, ) Running in standalone mode
|`-._`-...-` __...-.``-._|'` _.-'| Port: 0
| `-._ `._ / _.-' | PID: 9001
`-._ `-._ `-./ _.-' _.-'
|`-._`-._ `-.__.-' _.-'_.-'|
| `-._`-._ _.-'_.-' | http://redis.io
`-._ `-._`-.__.-'_.-' _.-'
|`-._`-._ `-.__.-' _.-'_.-'|
| `-._`-._ _.-'_.-' |
`-._ `-._`-.__.-'_.-' _.-'
`-._ `-.__.-' _.-'
`-._ _.-'
`-.__.-'
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis-server[9001]: 9001:M 28 Aug 2021 09:40:06.710 # Server initialized
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis[9001]: Server initialized
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis-server[9001]: 9001:M 28 Aug 2021 09:40:06.711 * The server is now ready to accept connections at /run/redis-openvas/redis>
Aug 28 09:40:06 bullseye.kifarunix-demo.com redis[9001]: The server is now ready to accept connections at /run/redis-openvas/redis.sock
Aug 28 09:40:06 bullseye.kifarunix-demo.com systemd[1]: Started Advanced key-value store (openvas).
Update Network Vulnerability Tests (NVTs)
Update Network Vulnerability Tests feed from Greenbone Security Feed/Community Feed using the greenbone-nvt-sync command. rsync tool is required for a successful synchronization.
Note that greenbone-nvt-sync must not be executed as privileged user root. For this reason, update the NVTs as gvm user created above.
Ensure that user can write to OpenVAS libraries directory, /var/lib/openvas/, directory.
chown -R gvm: /var/lib/openvas/Also, allow GVM user to run openvas with sudo rights.
echo "gvm ALL = NOPASSWD: $(which openvas)" >> /etc/sudoers.d/gvmNext, update the NVTs GVM user;
su - gvmgreenbone-nvt-syncIf the command fails with:
rsync: [receiver] read error: Connection reset by peer (104)
rsync error: error in socket IO (code 10) at io.c(784) [receiver=3.2.3]
rsync: connection unexpectedly closed (1913648 bytes received so far) [generator]
rsync error: error in rsync protocol data stream (code 12) at io.c(228) [generator=3.2.3]Then append --rsync option and rerun the command.
greenbone-nvt-sync --rsyncOnce the update is done, you need to upload the plugins into Redis server;
sudo openvas --update-vt-infoBuild and Install Greenbone Vulnerability Manager
cd gvm-source/gvmd
mkdir build && cd build
cmake ..
make
sudo make installBuild and Install Greenbone Security Assistant
The Greenbone Security Assistant is the web interface developed for the Greenbone Security Manager
cd ../../gsa
rm -rf build
yarn
yarn buildAll content of the production build can be shipped with every web server. For providing GSA via gsad web server, the files need to be copied into the /usr/local/share/gvm/gsad/web/.
Build and Install Greenbone Security Assistant HTTP server
The Greenbone Security Assistant HTTP Server is the server developed for the communication with the Greenbone Security Manager appliances. It connects to the Greenbone Vulnerability Manager Daemon gvmd to provide a full-featured user interface for vulnerability management.
cd ../../gsad
mkdir build && cd build
cmake ..
make
sudo make installNext, copy the web interface configs;
[[ -d /usr/local/share/gvm/gsad/web ]] || mkdir -p /usr/local/share/gvm/gsad/webchown -R gvm: /usr/local/share/gvm/gsad/webcp -rp /opt/gvm/gvm-source/gsa/build/* /usr/local/share/gvm/gsad/webKeeping the feeds up-to-date
The gvmd Data, SCAP and CERT Feeds should be kept up-to-date by calling the greenbone-feed-sync script regularly (e.g. via a cron entry):
exitchown -R gvm: /var/lib/gvm/sudo -u gvm greenbone-feed-sync --type GVMD_DATAsudo -u gvm greenbone-feed-sync --type SCAPsudo -u gvm greenbone-feed-sync --type CERTPlease note: The CERT feed sync depends on data provided by the SCAP feed and should be called after syncing the later.
Also, in case the commands fail with such an error;
rsync: read error: Connection reset by peer (104)
rsync error: error in socket IO (code 10) at io.c(794) [receiver=3.1.3]
rsync: connection unexpectedly closed (1047 bytes received so far) [generator]
rsync error: error in rsync protocol data stream (code 12) at io.c(235) [generator=3.1.3]Try adding --rsync option to the command, for example;
sudo -u gvm greenbone-feed-sync --type CERT --rsyncConsider setting cron jobs to run the nvts, cert and scap data update scripts at your preferred frequency to pull updates from the feed servers.
Generate GVM Certificates
Next, run the command below to generate certificates gvmd.
Server certificates are used for authentication while client certificates are primarily used for authorization. More on man gvm-manage-certs.
sudo -u gvm gvm-manage-certs -aBuild and Install OSPd and OSPd-OpenVAS
Open Scanner Protocol (OSP) creates a unified interface for different security scanners and makes their control flow and scan results consistently available under the central Greenbone Vulnerability Manager service.
su - gvmpip3 install wheel
pip3 install python-gvm gvm-toolscd /opt/gvm/gvm-source/ospd
python3 -m pip install .cd /opt/gvm/gvm-source/ospd-openvas
python3 -m pip install .Running OpenVAS Scanner, GSA and GVM services
In order to make the management of OpenVAS scanner, GSA (WebUI service) and GVM daemon, create systemd service unit files for each of them as follows.
Log out as gvm user and execute the commands below as a privileged user.
exitCreate Systemd Service unit for OpenVAS OSPD
You can copy the service unit file from the source directory to systemd service unit files directory and modify it accordingly. We use the service unit below in this setup.
cat > /etc/systemd/system/ospd-openvas.service << 'EOL'
[Unit]
Description=OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)
After=network.target networking.service [email protected] postgresql.service
[email protected]
ConditionKernelCommandLine=!recovery
[Service]
ExecStartPre=-rm -rf /var/run/gvm/ospd-openvas.pid /var/run/gvm/ospd-openvas.sock
Type=simple
User=gvm
Group=gvm
RuntimeDirectory=gvm
Environment=PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/opt/gvm/bin:/opt/gvm/sbin:/opt/gvm/.local/bin
ExecStart=/opt/gvm/.local/bin/ospd-openvas \
--pid-file /var/run/gvm/ospd-openvas.pid \
--log-file /var/log/gvm/ospd-openvas.log \
--lock-file-dir /var/run/gvm -u /var/run/gvm/ospd-openvas.sock
RemainAfterExit=yes
[Install]
WantedBy=multi-user.target
EOL
Set the user/group owner of the directories, /var/run/gvm and /var/log/gvm to user gvm.
[[ -d /var/run/gvm ]] || mkdir /var/run/gvmchown -R gvm: /var/run/gvm /var/log/gvmReload systemd configs;
systemctl daemon-reloadStart and enable OSPD openvas wrapper service;
systemctl enable --now ospd-openvasCheck the status;
systemctl status ospd-openvas.service● ospd-openvas.service - OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)
Loaded: loaded (/etc/systemd/system/ospd-openvas.service; enabled; vendor preset: enabled)
Active: active (exited) since Sat 2021-08-28 11:26:07 EAT; 6s ago
Process: 11142 ExecStartPre=rm -rf /var/run/gvm/ospd-openvas.pid /var/run/gvm/ospd-openvas.sock (code=exited, status=0/SUCCESS)
Process: 11143 ExecStart=/opt/gvm/.local/bin/ospd-openvas --pid-file /var/run/gvm/ospd-openvas.pid --log-file /var/log/gvm/ospd-openvas.log --lock-file-dir /var/run/gvm -u /ru>
Main PID: 11143 (code=exited, status=0/SUCCESS)
Tasks: 4 (limit: 4679)
Memory: 28.3M
CPU: 463ms
CGroup: /system.slice/ospd-openvas.service
├─11145 /usr/bin/python3 /opt/gvm/.local/bin/ospd-openvas --pid-file /var/run/gvm/ospd-openvas.pid --log-file /var/log/gvm/ospd-openvas.log --lock-file-dir /run/g>
└─11147 /usr/bin/python3 /opt/gvm/.local/bin/ospd-openvas --pid-file /var/run/gvm/ospd-openvas.pid --log-file /var/log/gvm/ospd-openvas.log --lock-file-dir /run/g>
Aug 28 11:26:07 bullseye.kifarunix-demo.com systemd[1]: Starting OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)...
Aug 28 11:26:07 bullseye.kifarunix-demo.com systemd[1]: Started OSPd Wrapper for the OpenVAS Scanner (ospd-openvas).
Be sure to also check the logs;
tail -f /var/log/gvm/ospd-openvas.logCreating Systemd Service units for GVM services
When run, the installer creates GVM daemon service unit, /lib/systemd/system/gvmd.service.
Let us modify this service unit file;
cp /lib/systemd/system/gvmd.service{,.bak}
cat > /lib/systemd/system/gvmd.service << 'EOL'
[Unit]
Description=Greenbone Vulnerability Manager daemon (gvmd)
After=network.target networking.service postgresql.service ospd-openvas.service
Wants=postgresql.service ospd-openvas.service
Documentation=man:gvmd(8)
ConditionKernelCommandLine=!recovery
[Service]
Type=forking
User=gvm
Group=gvm
RuntimeDirectory=gvmd
Environment=PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/opt/gvm/bin:/opt/gvm/sbin:/opt/gvm/.local/bin
ExecStart=/usr/local/sbin/gvmd --osp-vt-update=/var/run/gvm/ospd-openvas.sock
Restart=always
TimeoutStopSec=10
[Install]
WantedBy=multi-user.target
EOL
Reload system unit configs and start the services;
systemctl daemon-reload
systemctl enable --now gvmdChecking the status;
systemctl status gvmd
● gvmd.service - Greenbone Vulnerability Manager daemon (gvmd)
Loaded: loaded (/lib/systemd/system/gvmd.service; enabled; vendor preset: enabled)
Active: active (running) since Sat 2021-08-28 11:29:25 EAT; 1min 15s ago
Docs: man:gvmd(8)
Process: 11259 ExecStart=/usr/local/sbin/gvmd --osp-vt-update=/var/run/gvm/ospd-openvas.sock (code=exited, status=0/SUCCESS)
Main PID: 11261 (gvmd)
Tasks: 9 (limit: 4679)
Memory: 608.8M
CPU: 18.131s
CGroup: /system.slice/gvmd.service
├─11261 gvmd: Waiting for incoming connections
├─11299 gpg-agent --homedir /var/lib/gvm/gvmd/gnupg --use-standard-socket --daemon
├─11311 gvmd: Reloading NVTs
├─11312 gvmd: Syncing SCAP: Updating CPEs
├─11313 gvmd: OSP: Updating NVT cache
├─11314 gvmd: Syncing CERT
├─11326 sh -c xml_split -s40Mb split.xml && head -n 2 split-00.xml > head.xml && echo '' > tail.xml && for F in split-*.xml; do awk 'NR>3 {print>
├─11327 /usr/bin/perl -w /usr/bin/xml_split -s40Mb split.xml
└─11334 gvmd: Synchronizing feed data
Aug 28 11:29:25 bullseye.kifarunix-demo.com systemd[1]: Starting Greenbone Vulnerability Manager daemon (gvmd)...
Aug 28 11:29:25 bullseye.kifarunix-demo.com systemd[1]: Started Greenbone Vulnerability Manager daemon (gvmd).
Check the logs;
tail -f /var/log/gvm/gvmd.logCreating Systemd Service units for GSA services
When run, the installer creates GSA daemon service unit, /lib/systemd/system/gsad.service.
Let us modify this service unit file;
cp /lib/systemd/system/gsad.service{,.bak}
cat > /lib/systemd/system/gsad.service << 'EOL'
[Unit]
Description=Greenbone Security Assistant daemon (gsad)
Documentation=man:gsad(8) https://www.greenbone.net
After=network.target gvmd.service
Wants=gvmd.service
[Service]
Type=simple
User=gvm
Group=gvm
RuntimeDirectory=gsad
PIDFile=/var/run/gsad/gsad.pid
Environment=PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/opt/gvm/bin:/opt/gvm/sbin:/opt/gvm/.local/bin
ExecStart=/usr/bin/sudo /usr/local/sbin/gsad -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem
RemainAfterExit=yes
[Install]
WantedBy=multi-user.target
EOL
The option, -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem, is as per the certificates path generated by running the gvm-manage-certs command above.
Enable GVM user to run gsad with sudo rights;
echo "gvm ALL = NOPASSWD: $(which gsad)" >> /etc/sudoers.d/gvmReload system unit configs and start the services;
systemctl daemon-reload
systemctl enable --now gsadChecking the status;
systemctl status gsad● gsad.service - Greenbone Security Assistant daemon (gsad)
Loaded: loaded (/lib/systemd/system/gsad.service; enabled; vendor preset: enabled)
Active: active (exited) since Sat 2021-08-28 11:46:14 EAT; 55s ago
Docs: man:gsad(8)
https://www.greenbone.net
Process: 11954 ExecStart=/usr/bin/sudo /usr/local/sbin/gsad -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem (code=exited, status=0/SUCCESS)
Main PID: 11954 (code=exited, status=0/SUCCESS)
Tasks: 4 (limit: 4679)
Memory: 4.1M
CPU: 66ms
CGroup: /system.slice/gsad.service
├─11957 /usr/local/sbin/gsad -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem
└─11958 /usr/local/sbin/gsad -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem
Aug 28 11:46:14 bullseye.kifarunix-demo.com systemd[1]: Stopping Greenbone Security Assistant daemon (gsad)...
Aug 28 11:46:14 bullseye.kifarunix-demo.com sudo[11954]: gvm : PWD=/ ; USER=root ; COMMAND=/usr/local/sbin/gsad -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/g>
Aug 28 11:46:14 bullseye.kifarunix-demo.com systemd[1]: Started Greenbone Security Assistant daemon (gsad).
Aug 28 11:46:14 bullseye.kifarunix-demo.com sudo[11954]: pam_unix(sudo:session): session opened for user root(uid=0) by (uid=998)
Aug 28 11:46:15 bullseye.kifarunix-demo.com sudo[11955]: Oops, secure memory pool already initialized
Aug 28 11:46:15 bullseye.kifarunix-demo.com sudo[11954]: pam_unix(sudo:session): session closed for user root
Check the logs;
tail /var/log/gvm/gsad.logCreate GVM Scanner
Since we launched the scanner and set it to use our non-standard scanner host path (/var/run/gvm/ospd-openvas.sock), we need to create and register our scanner;
sudo -u gvm gvmd --create-scanner="Kifarunix-demo OpenVAS Scanner" \
--scanner-type="OpenVAS" --scanner-host=/var/run/gvm/ospd-openvas.sockScanner created.Next, you need to verify your scanner. For this, you first need to get the scanner identifier;
sudo -u gvm gvmd --get-scanners08b69003-5fc2-4037-a479-93b440211c73 OpenVAS /run/ospd/ospd-openvas.sock 0 OpenVAS Default
6acd0832-df90-11e4-b9d5-28d24461215b CVE 0 CVE
6e0c2bec-9688-430d-b8da-f59a7c27fbe7 OpenVAS /var/run/gvm/ospd-openvas.sock 9390 Kifarunix-demo OpenVAS Scanner
Based on the output above, our scanner UUID is, 6e0c2bec-9688-430d-b8da-f59a7c27fbe7.
Verify the scanner;
sudo -u gvm gvmd --verify-scanner=6e0c2bec-9688-430d-b8da-f59a7c27fbe7Command output;
Scanner version: OpenVAS 21.4.3~dev1~git-3e7b6d3f-openvas-21.04.Create GVM Admin User
Create GVM administrative user by running the command below;
sudo -u gvm gvmd --create-user adminThis command generates a random password for the user. See sample output below;
User created with password '3ae45864-0d6a-4a53-938f-730a1bb5d959'.If you want to create a user and at the same time create your own password;
sudo -u gvm gvmd --create-user USERNAME --password=PASSWORDOtherwise, you can reset the password of an already existing user;
sudo -u gvm gvmd --user=<USERNAME> --new-password=<PASSWORD>An administrator user can later create further users or administrators via clients like the Greenbone Security Assistant (GSA).
Set the Feed Import Owner
According to gvmd/INSTALL.md, certain resources that were previously part of the gvmd source code are now shipped via the feed. An example is the config “Full and Fast”.
gvmd will only create these resources if a “Feed Import Owner” is configured:
sudo -u gvm gvmd --modify-setting 78eceaec-3385-11ea-b237-28d24461215b --value <uuid_of_user>The UUIDs of all created users can be found using
sudo -u gvm gvmd --get-users --verboseSample output;
admin bb3bd8a6-6b77-464f-9f9b-1afe4835be15Then modify the gvmd settings with the user UUID.
sudo -u gvm gvmd --modify-setting 78eceaec-3385-11ea-b237-28d24461215b --value bb3bd8a6-6b77-464f-9f9b-1afe4835be15Accessing GVM 21.04 Web Interface
Greenbone Security Assistant (GSA) WebUI daemon opens port 443 and listens on all interfaces.
ss -altnp | grep 443LISTEN 0 1024 *:443 *:* users:(("gsad",pid=11957,fd=10))If firewall is running, open this port to allow external access.
ufw allow 443/tcpYou can now access GSA via the url https:<serverIP-OR-hostname>.
Accept the self-signed SSL warning and proceed.

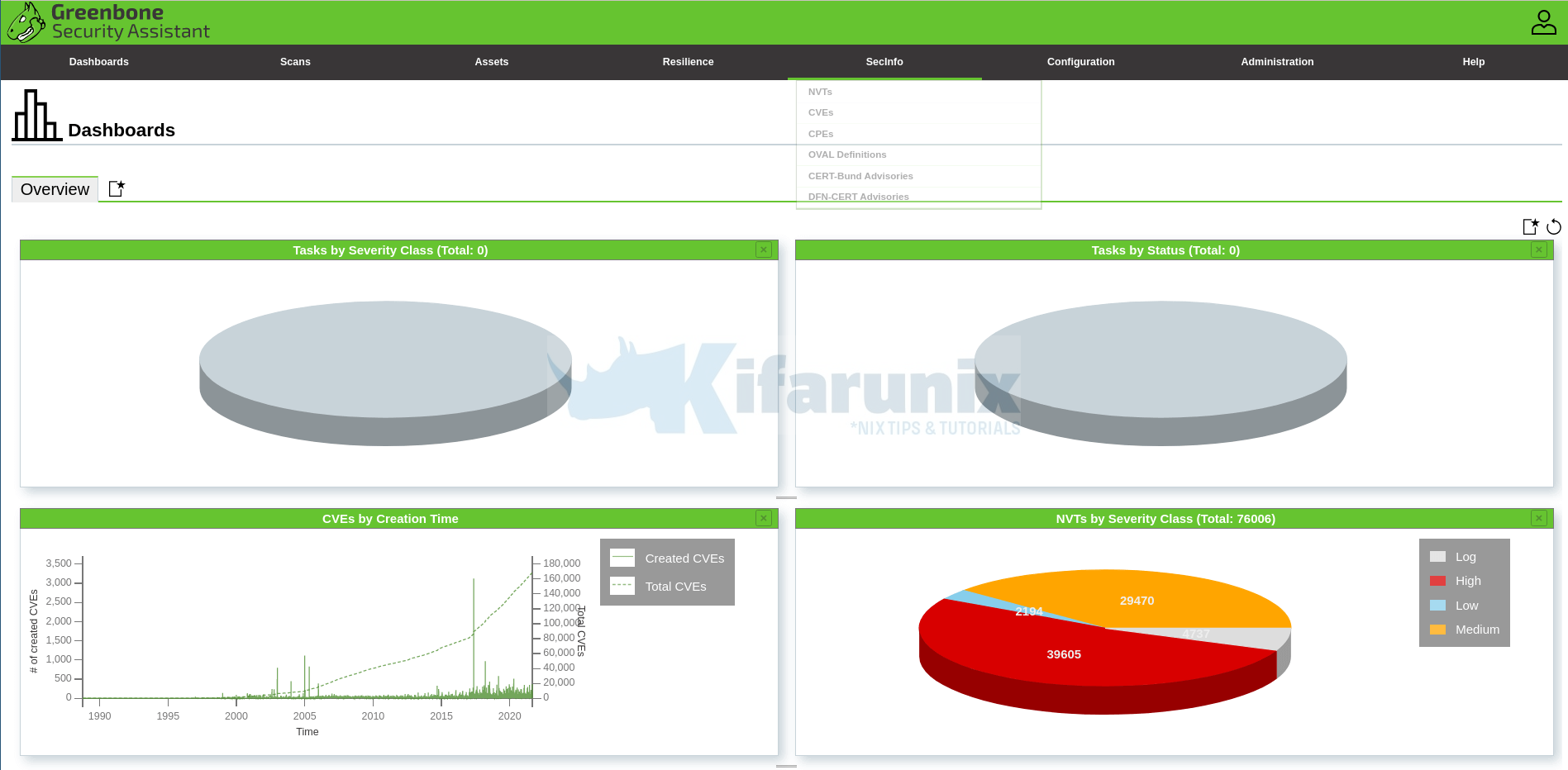
Dashboard
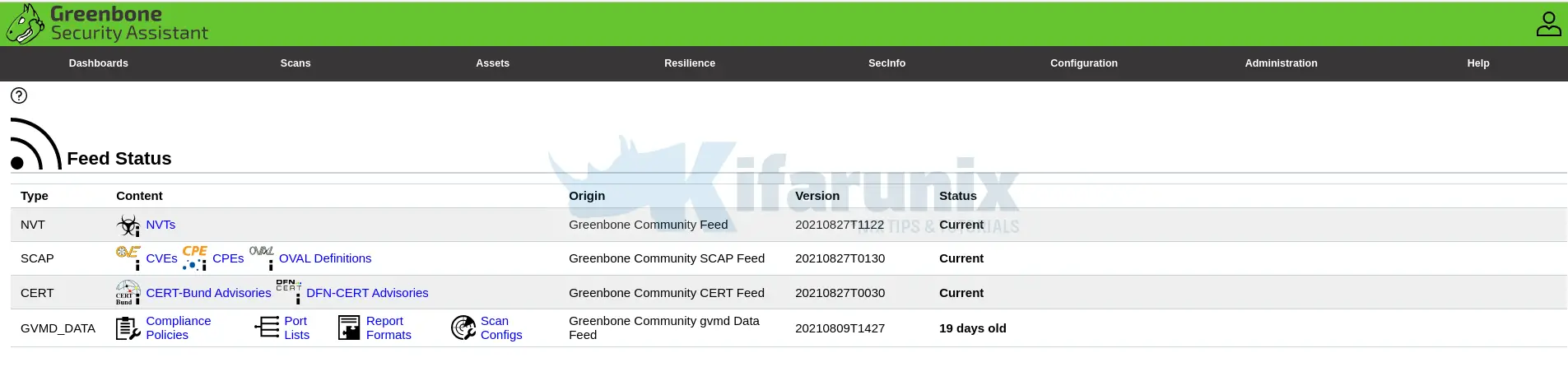
Feed Status
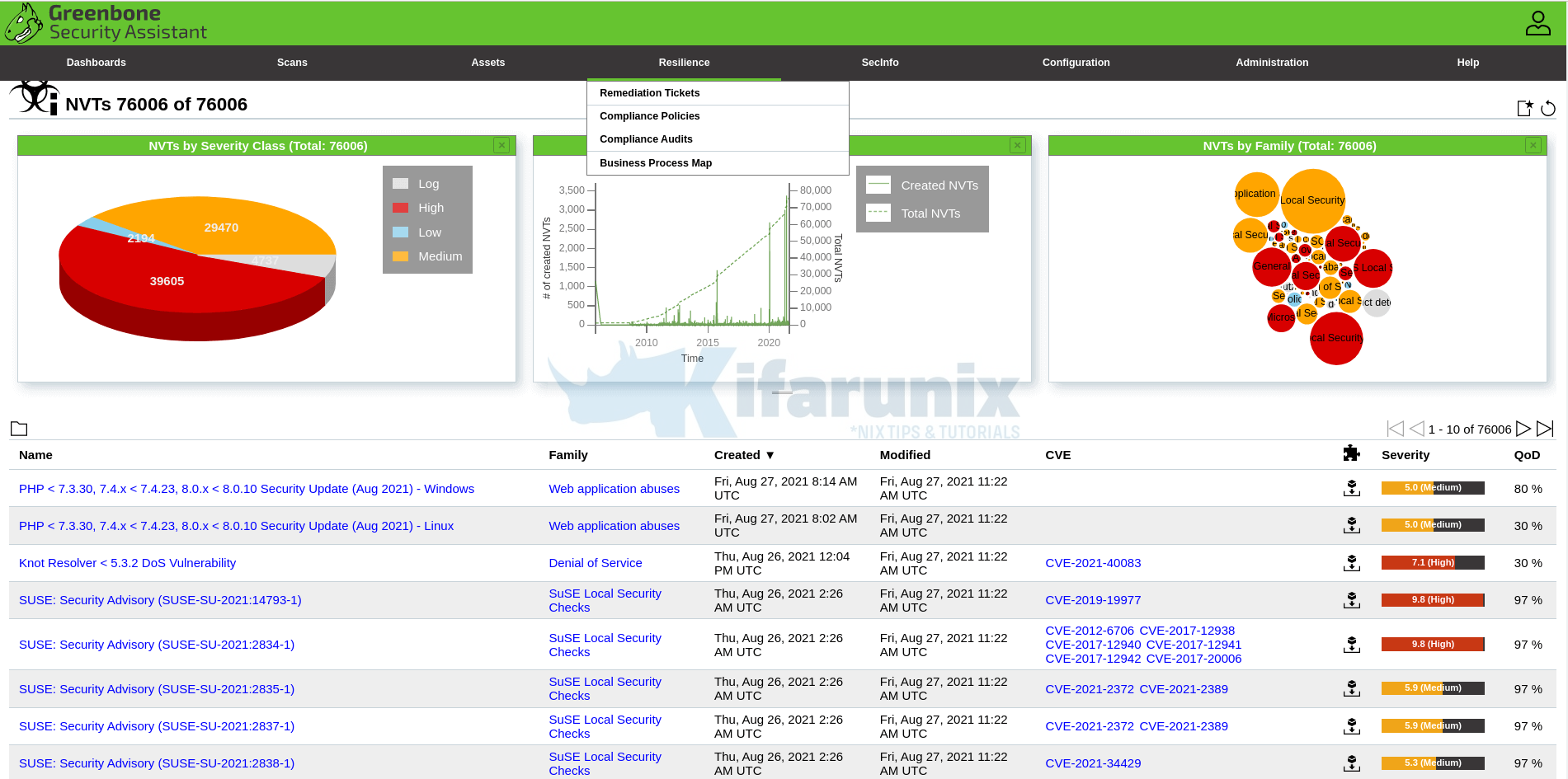
SecInfo
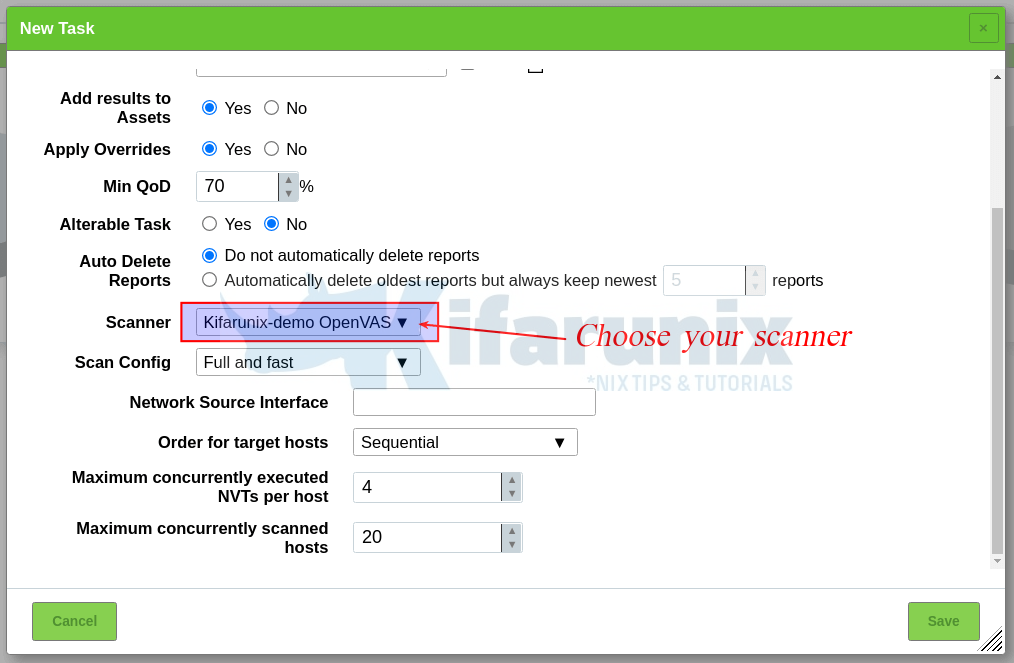
And hey, dont forget to choose your default scanner created above, when scanning your hosts;
You can now start scanning your assets.
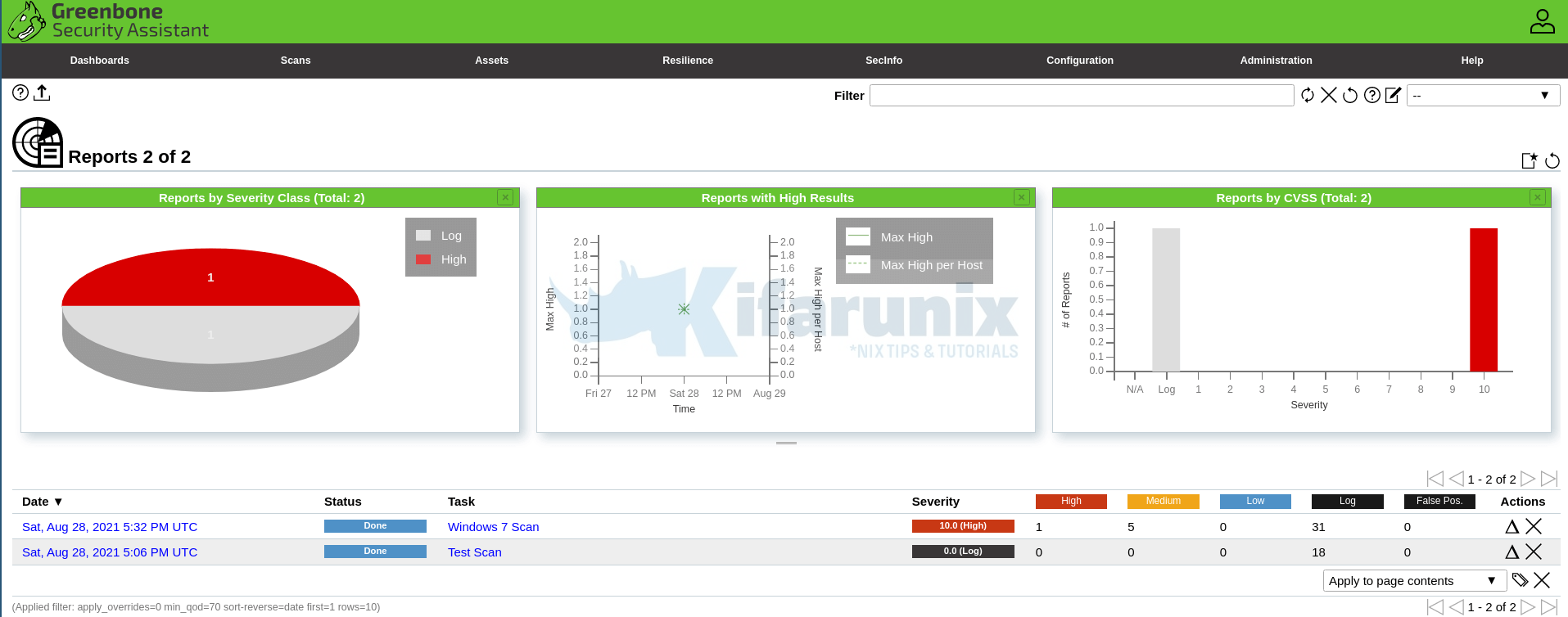
Sample Scan Report


I followed all steps, but when I scanned it pause in 0%. How can I process further?
Thanks and regards,
TT
Hi, how is your system resource consumption? What does the logs say?
Hi koromicha!
Thank you a lot for the guide!
During the installation it is not possible to start gvmd service. The error in /var/log/gvm/gvmd.log is:
md main:MESSAGE:2021-10-18 08h49.44 utc:91935: Greenbone Vulnerability Manager version 21.10.0~dev1~git-8a61b93d9-main (GIT revision 8a61b93d9-main) (DB revision 249)
md manage:WARNING:2021-10-18 08h49.44 utc:91936: sql_exec_internal: PQexec failed: ERROR: relation “public.meta” does not exist
LINE 1: SELECT value FROM public.meta WHERE name = ‘database_version…
^
(7)
md manage:WARNING:2021-10-18 08h49.44 utc:91936: sql_exec_internal: SQL: SELECT value FROM public.meta WHERE name = ‘database_version’;
md manage:WARNING:2021-10-18 08h49.44 utc:91936: sql_x: sql_exec_internal failed
md manage:MESSAGE:2021-10-18 08h49.44 utc:91936: No SCAP database found
md manage:MESSAGE:2021-10-18 08h49.44 utc:91936: No CERT database found
md manage:MESSAGE:2021-10-18 08h49.44 utc:91936: db_extension_available: Extension ‘pg-gvm’ is not available.
md manage:WARNING:2021-10-18 08h49.44 utc:91936: check_db_extensions: A required extension is not available.
md manage:WARNING:2021-10-18 08h49.44 utc:91936: init_manage_create_functions: failed to create functions
Can you help me?
Hi, I’m unable to clone the GVM github branch files:
~/gvm-source$ git clone -b gvm-libs-21.04 https://github.com/greenbone/gvm-libs.git
Cloning into ‘gvm-libs’…
fatal: Remote branch gvm-libs-21.04 not found in upstream origin
What can I do?
Hi, please check the source repository links listed here. See if it can help. We will get the team update the guide accordingly.
Thanks for letting us know, cheers!
git clone -b stable –single-branch https://github.com/greenbone/gvm-libs.git
git clone -b main –single-branch https://github.com/greenbone/openvas-smb.git
git clone -b stable –single-branch https://github.com/greenbone/openvas.git
git clone -b stable –single-branch https://github.com/greenbone/ospd.git
git clone -b stable –single-branch https://github.com/greenbone/ospd-openvas.git
git clone -b stable –single-branch https://github.com/greenbone/gvmd.git
git clone -b stable –single-branch https://github.com/greenbone/gsa.git
use this ones
thanks for this guide a great one if you have time to fight with few irregularities, such as missing branches. I may suggest not using the git in that case but tar archives as described here https://greenbone.github.io/docs/gvm-21.04/index.html#setting-up-postgresql. however, they are missing the part of redis optimization (especially THP)
git clone -b stable –single-branch https://github.com/greenbone/gvm-libs.git
fatal: 版本庫 ‘–single-branch’ 不存在
Cloning into ‘gvm-libs’…
fatal: Remote branch gvm-libs-21.04 not found in upstream origin
What can I do?
git clone -b main -–single-branch https://github.com/greenbone/gvm-libs.git
hi, while running–> cmake .. -DCMAKE_INSTALL_PREFIX=/opt/gvm in gvm-libs
i got below error,
/usr/bin/cmake -E cmake_link_script CMakeFiles/cmTC_72d77.dir/link.txt –verbose=1
/usr/bin/cc -DCMAKE_HAVE_LIBC_PTHREAD -rdynamic CMakeFiles/cmTC_72d77.dir/src.c.o -o cmTC_72d77
/usr/bin/ld: CMakeFiles/cmTC_72d77.dir/src.c.o: in function `main’:
src.c:(.text+0x46): undefined reference to `pthread_create’
/usr/bin/ld: src.c:(.text+0x52): undefined reference to `pthread_detach’
/usr/bin/ld: src.c:(.text+0x63): undefined reference to `pthread_join’
collect2: error: ld returned 1 exit status
make[1]: *** [CMakeFiles/cmTC_72d77.dir/build.make:87: cmTC_72d77] Error 1
make[1]: Leaving directory ‘/opt/gvm/gvm-source/gvm-libs/build/CMakeFiles/CMakeTmp’
can you pls help
Hi there
What to do?
CMake Error: The source directory “/opt/gvm/gvm-source/gsa” does not appear to contain CMakeLists.txt.
pls help me
change gsa on git clone to gsad
Thx Cicero for the tip
Another Problem:
root@debian11:~# systemctl start gvmd.service –> openvas21 systemd[1]: Failed to start Greenbone Vulnerability Manager daemon (gvmd).
tail -f /var/log/gvm/gvmd.log –> Failed to open lock file ‘/run/gvmd/gvm-checking’: Permission denied
ls -l /run/ –> drwxr-xr-x 2 root root 40 Nov 29 11:37 gvmd
did i missed something?
Change permission from folder
chown -R gvm: /run/gvmd
Thanks Augusto that worked, but that’s not part of this guide, am I right?
where you see:
echo “db_address = /run/redis/redis.sock” > /etc/openvas/openvas.conf
change for:
echo “db_address = /run/redis-openvas/redis.sock” > /etc/openvas/openvas.conf
During “Creating Systemd Service units for GSA services” (actually it is GSAD)
add the following steps (run as root):
mkdir -p /usr/local/share/gvm/gsad/web
cp -r -p /opt/gvm/gvm-source/gsad/build/* /usr/local/share/gvm/gsad/web
Then you will be able to run gsad.service:
systemctl daemon-reload
systemctl enable –now gsad
systemctl status gsad
add the following steps (run as root):
mkdir -p /usr/local/share/gvm/gsad/web
cp -r -p /opt/gvm/gvm-source/gsad/build/* /usr/local/share/gvm/gsad/web
I am still getting URL not found. gsad.service is running. gsad log says MHD: Error: received handshake message out of context.
Any suggestion how to fix this?
Hi, ensure that you build the GSA and copy the web interface files accordingly. Check the guide again on Building the GSA
1.
where you see:
echo “db_address = /run/redis/redis.sock” > /etc/openvas/openvas.conf
change for:
echo “db_address = /run/redis-openvas/redis.sock” > /etc/openvas/openvas.conf
2.
During “Creating Systemd Service units for GSA services” (actually it is GSAD)
add the following steps (run as root):
mkdir -p /usr/local/share/gvm/gsad/web
cp -r -p /opt/gvm/gvm-source/gsad/build/* /usr/local/share/gvm/gsad/web
Then you will be able to run gsad.service:
systemctl daemon-reload
systemctl enable –now gsad
systemctl status gsad
1.
where you see:
echo “db_address = /run/redis/redis.sock” > /etc/openvas/openvas.conf
change for:
echo “db_address = /run/redis-openvas/redis.sock” > /etc/openvas/openvas.conf
2.
During “Creating Systemd Service units for GSA services” (actually it is GSAD)
add the following steps (run as root):
mkdir -p /usr/local/share/gvm/gsad/web
cp -r -p /opt/gvm/gvm-source/gsad/build/* /usr/local/share/gvm/gsad/web
Then you will be able to run gsad.service:
systemctl daemon-reload
systemctl enable –now gsad
systemctl status gsad
3.
where you see:
“tail /usr/local/var/log/gvm/gsad.log”
change to:
“tail -f /var/log/gvm/gsad.log”
Finished the installation and when accessing the WebUI “The Greenbone Vulnerability Manager service is not responding. This could be due to system maintenance. Please try again later, check the system status, or contact your system administrator.” The admin password has been changed and the error continues.
I get the following log:
root@server:~# tail -f /usr/local/var/log/gvm/gsad.log
gsad gmp:WARNING:2021-12-01 15h19.06 utc:26369: Failed to connect to server at /run/gvm/gvmd.sock: No such file or directory
gsad gmp:WARNING:2021-12-01 15h19.06 utc:26369: Authentication failure for ‘admin’ from 10.1.1.179. Status was 1.
gsad main:WARNING:2021-12-01 15h26.34 utc:26369: MHD: Error: received handshake message out of context.
gsad main:WARNING:2021-12-01 15h26.55 utc:26369: MHD: Error: received handshake message out of context.
gsad gmp:WARNING:2021-12-01 15h27.45 utc:26369: Failed to connect to server at /run/gvm/gvmd.sock: No such file or directory
gsad gmp:WARNING:2021-12-01 15:27.45 utc:26369: Authentication failure for ‘admin’ from 10.1.1.179. Status was 1.
gsad main:MESSAGE:2021-12-01 15h53.25 utc:29491: Starting GSAD version 21.4.3
gsad main:MESSAGE:2021-12-01 15:54.29 utc:29588: Starting GSAD version 21.4.3
gsad gmp:WARNING:2021-12-01 15:55.07 utc:29589: Failed to connect to server at /run/gvm/gvmd.sock: No such file or directory
gsad gmp:WARNING:2021-12-01 15:55.07 utc:29589: Authentication failure for ‘admin’ from 10.1.1.179. Status was 1.
gsad gmp:WARNING:2021-12-01 15h56.34 utc:29589: Failed to connect to server at /run/gvm/gvmd.sock: No such file or directory
gsad gmp:WARNING:2021-12-01 15h56.34 utc:29589: Authentication failure for ‘admin’ from 10.1.1.179. Status was 1.
You need to change the change the –munix-socket parameter during the Cmake, or you can change it within the /lib/systemd/system/gsad.service in “ExecStart=…. –munix-socket=/var/run/gvmd/gvmd.sock”
if (of course) you have the gvmd.sock at /var/run/gvmd. If not, just find it, and change it appropriately.
the you just need to systemctl daemon-reload
and systemctl restart gsad.service
my exec is like this: “/usr/local/sbin/gsad -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem –munix-socket=/var/run/gvmd/gvmd.sock”
Jozef
Next Install Problem
systemctl status gsad –> g_lstat(/usr/local/share/gvm/gsad) failed – No such file or directory
as mentioned in this guide:
Check the logs;
tail /usr/local/var/log/gvm/gsad.log –> there is no log file there, i found the log file in “/var/log/gvm/gsad.log”
anyway in the gsad.log
gsad main:MESSAGE:2021-12-09 14h16.25 utc:81029: Starting GSAD version 21.4.3
gsad main:WARNING:2021-12-09 14h16.25 utc:81031: MHD: Failed to bind to port 80: Address already in use
gsad main:WARNING:2021-12-09 14h16.25 utc:81031: main: start_http_daemon redirect failed !
gsad main:CRITICAL:2021-12-09 14h16.25 utc:81030: chroot_drop_privileges: failed to change to “/usr/local/share/gvm/gsad/web”: No such file or directory
gsad main:CRITICAL:2021-12-09 14h16.25 utc:81030: main: Cannot use drop privileges for directory “web”!
is this guide still up to date???
Hi man
I relate for the beautiful tutorial.
I need help. I stopped in the part of: SystemCTL Enable –Now GVMD. Because I’m getting the following message:
md manage:WARNING:2021-12-16 18h46.33 utc:1292: Failed to open lock file ‘/run/gvmd/gvm-checking’: Arquivo ou diretório inexistente
md main:CRITICAL:2021-12-16 18h46.33 utc:1292: gvmd: Error trying to get checking lock
Hi,
Change permission from folder
chown -R gvm: /run/gvmd
and systemctl restart gvmd.service
Hi!
sorry, I may be wrong.
the /run on debian is tmpfs and it have to be recreated every restart.
Are there some fix for it?
Yes, check how you can use
RuntimeDirectoryon the systemd unit file to the service that requires some directory under /run to create it on boot.Hi,
I have completed all the installations, but I cannot reach the web interface.
Error message: URL not found The requested URL is not available
root@debian:/lib/systemd/system# tail -f /var/log/gvm/gsad.log
gsad main:WARNING:2022-01-06 09h08.08 utc:60349: MHD: Error: received handshake message out of context.
gsad main:WARNING:2022-01-06 09h08.08 utc:60349: MHD: Error: received handshake message out of context.
gsad main:WARNING:2022-01-06 09h08.08 utc:60349: MHD: Error: received handshake message out of context.
gsad main:WARNING:2022-01-06 09h08.08 utc:60349: MHD: Error: received handshake message out of context.
gsad main:WARNING:2022-01-06 09h08.08 utc:60349: MHD: Error: received handshake message out of context.
gsad main:MESSAGE:2022-01-06 09h33.34 utc:61046: Starting GSAD version 21.4.3
gsad main:WARNING:2022-01-06 09h34.05 utc:61047: MHD: Error: received handshake message out of context.
Any help is appreciated
add the following steps (run as root):
mkdir -p /usr/local/share/gvm/gsad/web
cp -r -p /opt/gvm/gvm-source/gsad/build/* /usr/local/share/gvm/gsad/web
Then you will be able to run gsad.service:
systemctl daemon-reload
systemctl enable –now gsad
systemctl status gsad
GSAD is “only” the web server, you stil need to install/create the web itself and copy it to the gsad web folder (in my case /usr/local/share/gvm/gsad/web/)
see https://github.com/greenbone/gsa/blob/main/README.md
Hi
I followed the tuto
and I have a problem on this command line.
cd /opt/gvm/gvm-source/ospd-openvas
python3 -m pip install .
FileNotFoundError: [Errno 2] No such file or directory: ‘/tmp/pip-req-build- irwzz7_m/setup.py’
Is it a problem of right ?
I discover Linux and these tutorials allow me to progress
thank you for your ideas
Richard
Dear great tutorial ..please help ..
i can’t access to gvm user when i type
su – gvm can’t discover password..
When doing the make on openvas
[ 75%] Building C object nasl/CMakeFiles/openvas_nasl_shared.dir/time.c.o
[ 76%] Linking C shared library libopenvas_nasl.so
[ 76%] Built target openvas_nasl_shared
Scanning dependencies of target openvas-nasl
[ 77%] Building C object nasl/CMakeFiles/openvas-nasl.dir/nasl.c.o
[ 79%] Linking C executable openvas-nasl
/usr/bin/ld: libopenvas_nasl.so.21.4.4~dev1~git-f64afcb0-stable: undefined reference to `nvti_set_timeout’
collect2: error: ld returned 1 exit status
make[2]: *** [nasl/CMakeFiles/openvas-nasl.dir/build.make:86: nasl/openvas-nasl] Error 1
make[1]: *** [CMakeFiles/Makefile2:282: nasl/CMakeFiles/openvas-nasl.dir/all] Error 2
make: *** [Makefile:163: all] Error 2
@Richard, I had the same error and fixed it py upgrading pip and setuptools.
Run these commands as the gvm user:
python3 -m pip install -U pip
python3 -m pip install -U setuptools
Congrets for this wonderful works!
Thanks! Fantastic job. But I have a problem, could you help
when I use systemctl enable –now gsad
I see
gsad main:MESSAGE:2022-03-31 17h57.37 utc:22769: Starting GSAD version 21.4.5~dev1
gsad main:CRITICAL:2022-03-31 17h57.37 utc:22770: main: Could not write PID file.
root@openvas:~# systemctl status gvmd
● gvmd.service – Greenbone Vulnerability Manager daemon (gvmd)
Loaded: loaded (/lib/systemd/system/gvmd.service; enabled; vendor preset: enabled)
Active: failed (Result: exit-code) since Mon 2022-08-08 17:50:05 -03; 35s ago
Docs: man:gvmd(8)
Process: 22456 ExecStart=/usr/local/sbin/gvmd –osp-vt-update=/var/run/gvm/ospd-openvas.sock (code>
Main PID: 22457 (code=exited, status=1/FAILURE)
CPU: 36ms
ago 08 17:50:05 openvas systemd[1]: gvmd.service: Scheduled restart job, restart counter is at 5.
ago 08 17:50:05 openvas systemd[1]: Stopped Greenbone Vulnerability Manager daemon (gvmd).
ago 08 17:50:05 openvas systemd[1]: gvmd.service: Start request repeated too quickly.
ago 08 17:50:05 openvas systemd[1]: gvmd.service: Failed with result ‘exit-code’.
ago 08 17:50:05 openvas systemd[1]: Failed to start Greenbone Vulnerability Manager daemon (gvmd).
– Build and install the pg-gvm extension
$ cd /opt/gvm/gvm-source
$ git clone -b stable –single-branch https://github.com/greenbone/pg-gvm.git
$ cd pg-gvm
$ mkdir build && cd build
$ cmake ..
$ make
$ sudo make install
Then restart postgresql and gvmd services and it should be working
Same problem like Douglas Augusto has.
md manage:WARNING:2022-08-24 13h32.44 utc:41798: sql_exec_internal: SQL: SELECT value FROM public.meta WHERE name = ‘database_version’;
md manage:WARNING:2022-08-24 13h32.44 utc:41798: sql_x: sql_exec_internal failed
md manage:MESSAGE:2022-08-24 13h32.44 utc:41798: No SCAP database found
md manage:MESSAGE:2022-08-24 13h32.44 utc:41798: No CERT database found
md manage:MESSAGE:2022-08-24 13h32.44 utc:41798: db_extension_available: Extension ‘pg-gvm’ is not available.
md manage:WARNING:2022-08-24 13h32.44 utc:41798: check_db_extensions: A required extension is not available.
md manage:WARNING:2022-08-24 13h32.44 utc:41798: init_manage_create_functions: failed to create functions
md main:MESSAGE:2022-08-24 13h32.44 utc:41802: Greenbone Vulnerability Manager version 22.4.0~dev1~git-f35abf80-stable (GIT revision f35abf80-stable) (DB revision 250)
md manage:WARNING:2022-08-24 13h32.44 utc:41803: sql_exec_internal: PQexec failed: ERROR: relation “public.meta” does not exist
LINE 1: SELECT value FROM public.meta WHERE name = ‘database_version…
Same problem as Vasilius, Douglas Augusto and Alex.
Any updates on this?
Hey, thank you for this wonderful howto!
I failed to compile on Debian12 “bookworm” with your instruction and got errors compiling gvmd on the psql-part. Installed specific version 11 and 13 to no avail…
Searched through the forum and the issue-tracker and found an answer: https://github.com/greenbone/gvmd/issues/2017#issuecomment-1600975455
Cloned all repos again without branch-specification and all went fine! Consider removing the pull from stable/main branches