In this guide, you will learn how to install GVM 21.04 on Rocky Linux 8. Greenbone Vulnerability Management (GVM), previously known as OpenVAS, is a network security scanner which provides a set of network vulnerability tests (NVTs) to detect security loopholes in systems and applications. As of this writing, GVM 21.04 is the current stable release.
Want to use Debian 11 instead? Use the guide below;
Install GVM 21.04 on Debian 11/Debian 10
Install GVM on Rocky Linux 8
Prerequisites
In this demo, we will install and setup GVM 21.04 on Rocky Linux 8 from source code. As such, below are the system requirements I would personally recommend.
- At least 4 GB RAM
- At least 4 vCPUs
- More than 8 GB disk space (We used 16 GB in this demo)
These requirements will vary depending on your use cases, however. Just be sure to provide “enough”.
DISCLAIMER: I cannot guarantee you that this guide will work for you out of the box. So just try it.
Run System Update
To begin with, update and upgrade your system packages;
dnf updateCreate GVM User on Rocky Linux
In this demo, we will run GVM 21.04 as a non privileged system user. Thus, create gvm system user account.
useradd -r -d /opt/gvm -c "GVM User" -s /bin/bash gvmCreate the GVM user directory as specified by option -d in the command above and set the user and group ownership to gvm.
mkdir /opt/gvm && chown gvm: /opt/gvmInstall Required Build Tools
In order to successfully build GVM 21.04 on Rocky Linux 8, you need to install a number of required dependencies and build tools.
Enable repositories that will provide additional packages;
dnf install epel-release -ydnf config-manager --set-enabled powertoolsNext, Install the required build tools.
dnf group install "Development Tools"dnf install cmake glib2-devel zlib-devel gnutls-devel libuuid-devel libssh-devel libxml2-devel wget vim rsync \
libgcrypt-devel openldap-devel popt-devel redis libical-devel openssl-devel hiredis-devel radcli-devel bzip2-devel \
python3-devel libpq-devel texinfo xmltoman nmap sshpass socat mingw32-gcc ncurses-devel libunistring-devel xz-devel \
gpgme-devel libksba-devel doxygen libpcap-devel python3-polib libmicrohttpd-devel gnutls-utils libnet-devel libffi-develBuilding OpenVAS SMB requires Heimdal GSSAPI package. You need to build this package from the source.
Download Heimdal package from the releases page.
wget https://github.com/heimdal/heimdal/releases/download/heimdal-7.7.0/heimdal-7.7.0.tar.gz -P /tmp/Extract and install Heimdal on Rocky Linux 8;
cd /tmptar xzf heimdal-7.7.0.tar.gz
cd heimdal-7.7.0
./configure --enable-opt=no --disable-otp --prefix=/opt/heimdal
make
make install
cd ~ln -s /opt/heimdal/include/ /opt/heimdal/include/heimdal
echo "/opt/heimdal/lib" > /etc/ld.so.conf.d/heimdal-gssapi.conf
ldconfigNext, create a symbolic of the /usr/lib64/libtspi.so.1 to /usr/lib64/libtspi.so. This is needs to be done to fix the error, /usr/bin/ld: cannot find -ltspi, encountered while compiling OpenVAS SMB.
ln -s /usr/lib64/libtspi.so.1 /usr/lib64/libtspi.soInstall Python >=3.7 required to build OSPD. We choose to install Python 3.7.9 in this demo;
wget https://www.python.org/ftp/python/3.7.9/Python-3.7.9.tgztar xzf Python-3.7.9.tgz
cd Python-3.7.9
./configure --enable-optimizations
make altinstall
cd ~Configure SELinux
In this demo, we have set up SELinux to run in permissive mode. I don’t recommend this, though. But i couldn’t deal with various permissions!
setenforce 0sed -i 's/=enforcing/=permissive/' /etc/selinux/configAllow gvm user to run installation with passwordless sudo;
echo "gvm ALL = NOPASSWD: $(which make) install" > /etc/sudoers.d/gvmInstall Yarn on Rocky Linux 8
Next, install Yarn JavaScript package manager by following the link below;
Install PostgreSQL on Rocky Linux 8
GVM 21.04 uses PostgreSQL as the backend database. Hence, run the command below to install PostgreSQL on Rocky Linux 8.
sudo dnf -y install -y postgresql-server postgresql-contrib postgresql-server-develOnce the installation is done, Initialize:
/usr/bin/postgresql-setup --initdbNext, start it and enable it to run on system boot;
systemctl enable --now postgresqlCreate PostgreSQL User and Database
Once the installation is done, create the PostgreSQL user and database for Greenbone Vulnerability Management Daemon (gvmd).
Note that the database and user should be created as PostgreSQL user, postgres.
sudo -Hiu postgres
createuser gvm
createdb -O gvm gvmdGrant PostgreSQL User DBA Roles
psql gvmd
create role dba with superuser noinherit;
grant dba to gvm;
\q
exitOnce that is done, restart PostgreSQL;
systemctl restart postgresqlCreate a symbolic link;
ln -s /usr/include /usr/include/postgresqlBuilding GVM 21.04 from Source
There are different tools required to install and setup GVM 21.04 on Rocky Linux 8. These include;
- GVM Libraries
- OpenVAS Scanner
- OSPd
- ospd-openvas
- Greenbone Vulnerability Manager
- Greenbone Security Assistant
- Python-GVM
- GVM-Tools
- OpenVAS SMB
Every component has README.md and a INSTALL.md file that explains how to build and install it.
Since we are running GVM as non-privileged user, gvm, then we will install all the GVM configuration files and libraries under, /opt/gvm.
Update the PATH environment variable on /etc/environment, to include the GVM binary path such that it looks like;
echo "PATH=$PATH:/opt/gvm/bin:/opt/gvm/sbin:/opt/gvm/.local/bin" >> /etc/environmentsource /etc/environmentAdd GVM library path to /etc/ld.so.conf.d.
echo "/opt/gvm/lib" > /etc/ld.so.conf.d/gvm.confInstall and Setup GVM 21.04 on Rocky Linux 8
Switch to GVM user, gvm and create a temporary directory to store GVM source files.
su - gvmmkdir gvm-sourceDownload GVM 21.04 Source Files
Navigate to temporary directory created above and run the subsequent commands to clone the GVM github branch files.
cd gvm-sourcegit clone -b stable --single-branch https://github.com/greenbone/gvm-libs.gitgit clone -b main --single-branch https://github.com/greenbone/openvas-smb.gitgit clone -b stable --single-branch https://github.com/greenbone/openvas.gitgit clone -b stable --single-branch https://github.com/greenbone/ospd.gitgit clone -b stable --single-branch https://github.com/greenbone/ospd-openvas.gitgit clone -b stable --single-branch https://github.com/greenbone/gvmd.gitgit clone -b stable --single-branch https://github.com/greenbone/gsa.gitOnce the source files are in place, proceed to build and install GVM on Rocky Linux
Note the current working directory;
pwd/opt/gvm/gvm-sourcels -1gsa
gvmd
gvm-libs
openvas
openvas-smb
ospd
ospd-openvasNote that we will install all GVM 21.04 files and libraries to a non-standard location, /opt/gvm.
As such, you need to set the PKG_CONFIG_PATH environment variable to the location of your pkg-config files before running the installation.
Pay attention to the export command.
Be sure to replace the path, /opt/gvm, accordingly.
Build and Install GVM 11 Libraries
From within the source directory, /opt/gvm/gvm-source, in this setup, change to GVM libraries directory;
cd gvm-libs
mkdir build && cd build
export PKG_CONFIG_PATH=/opt/gvm/lib/pkgconfig:$PKG_CONFIG_PATH
cmake .. -DCMAKE_INSTALL_PREFIX=/opt/gvm
make
sudo make installBuild and Install OpenVAS scanner and OpenVAS SMB
Open Vulnerability Assessment Scanner (OpenVAS) is a full-featured scan engine that executes a continuously updated and extended feed of Network Vulnerability Tests (NVTs).
OpenVAS SMB provides modules for the OpenVAS Scanner to interface with Microsoft Windows Systems through the Windows Management Instrumentation API and a winexe binary to execute processes remotely on that system.
Build and install openvas-smb;
cd ../../openvas-smb/
mkdir build && cd build
export PKG_CONFIG_PATH=/opt/gvm/lib/pkgconfig:/opt/heimdal/lib/pkgconfig:$PKG_CONFIG_PATH
cmake .. -DCMAKE_INSTALL_PREFIX=/opt/gvm
make
sudo make installBuild and install OpenVAS scanner;
cd ../../openvas
mkdir build && cd build
cmake .. -DCMAKE_INSTALL_PREFIX=/opt/gvm
make
make installConfiguring OpenVAS Scanner
The host scan information is stored temporarily on Redis server. The default configuration of Redis server is /etc/redis/redis.conf.
Switch back to privileged user and proceed.
exitTo begin run the command below to create the cache to the installed shared libraries;
ldconfigNext, copy OpenVAS scanner Redis configuration file, redis-openvas.conf, to the same Redis configuration file;
mv /etc/redis.conf{,.original}cp /opt/gvm/gvm-source/openvas/config/redis-openvas.conf /etc/redis.confUpdate the ownership of the configuration.
chown redis: /etc/redis.confUpdate the path to Redis unix socket on the /etc/redis.conf:
sed -i 's#/run/redis-openvas/redis.sock#/tmp/redis.sock#' /etc/redis.confSimilarly, specify the path to Redis socket file on the /etc/openvas/openvas.conf configuration file using the db_address parameter as follows.
echo "db_address = /tmp/redis.sock" > /etc/openvas/openvas.confchown gvm: /etc/openvas/openvas.confAdd gvm user to redis group;
usermod -aG redis gvmYou can also optimize Redis server itself improve the performance by making the following adjustments;
Increase the value of somaxconn in order to avoid slow clients connections issues.
echo "net.core.somaxconn = 1024" >> /etc/sysctl.confRedis background save may fail under low memory condition. To avoid this, enable memory overcommit (man 5 proc).
echo 'vm.overcommit_memory = 1' >> /etc/sysctl.confReload sysctl variables created above.
sysctl -pTo avoid creation of latencies and memory usage issues with Redis, disable Linux Kernel’s support for Transparent Huge Pages (THP). To easily work around this, create a systemd service unit for this purpose.
cat > /etc/systemd/system/disable_thp.service << 'EOL'
[Unit]
Description=Disable Kernel Support for Transparent Huge Pages (THP)
[Service]
Type=simple
ExecStart=/bin/sh -c "echo 'never' > /sys/kernel/mm/transparent_hugepage/enabled && echo 'never' > /sys/kernel/mm/transparent_hugepage/defrag"
[Install]
WantedBy=multi-user.target
EOL
Reload systemd configurations;
systemctl daemon-reloadStart and enable this service to run on system boot.
systemctl enable --now disable_thpStart and enable Redis to run on system boot;
systemctl enable --now redisA number of Network Vulnerability Tests (NVTs) require root privileges to perform certain operations. Since openvas is launched from an ospd-openvas process, via sudo, add the line below to sudoers file to ensure that the gvm user used in this demo can run the openvas with elevated rights using passwordless sudo.
echo "gvm ALL = NOPASSWD: /opt/gvm/sbin/openvas" > /etc/sudoers.d/gvmAlso, update the secure_path to include the GVM /sbin paths, /opt/gvm/sbin.
sed -i.bak '/secure_path/ s|$|:/opt/gvm/sbin|' /etc/sudoersUpdate NVTs
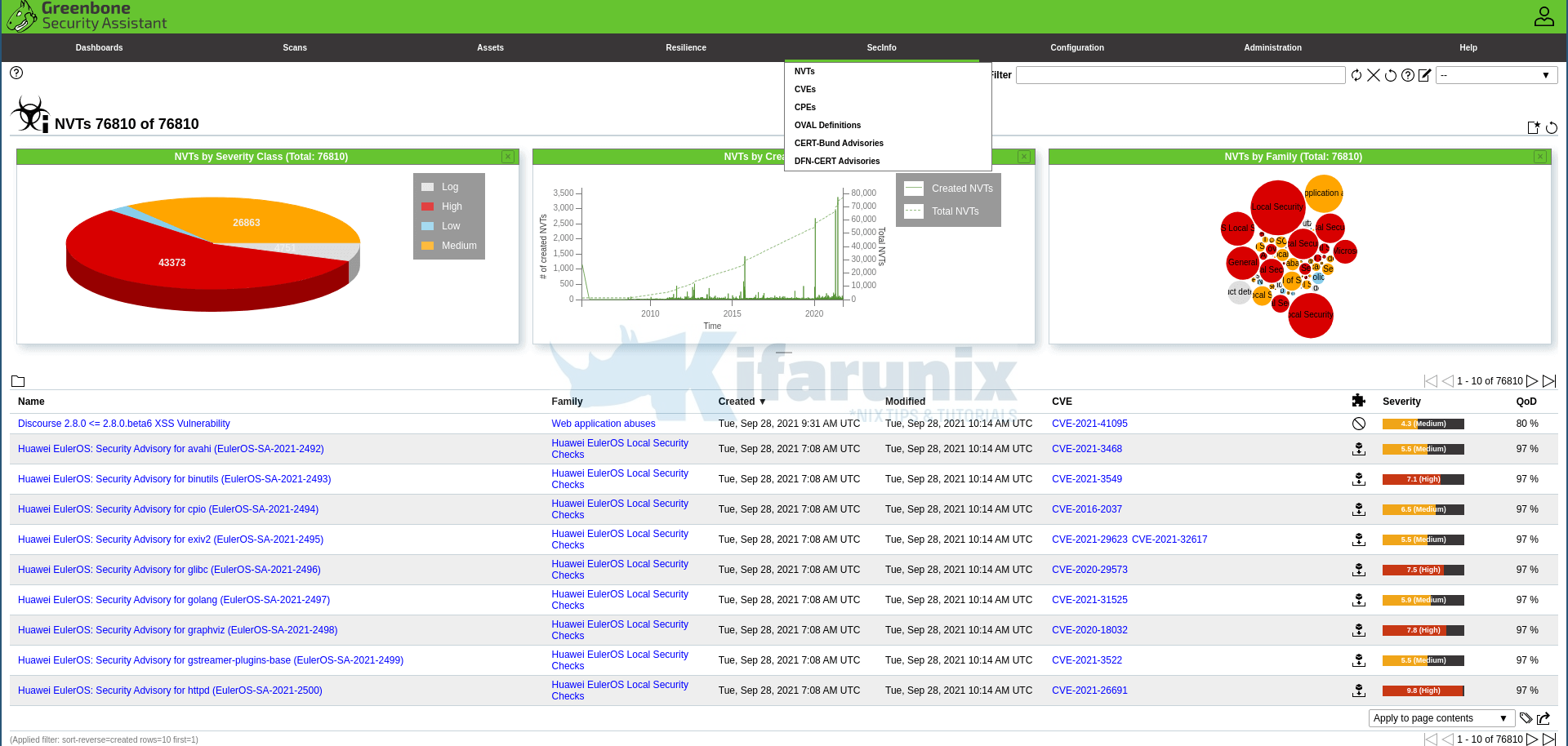
Update Network Vulnerability Tests feed from Greenbone Security Feed/Community Feed using the greenbone-nvt-sync command.
The greenbone-nvt-sync command must not be executed as privileged user root, hence switch back to GVM user we created above and update the NVTs.
Ensure that user can write to OpenVAS libraries directory, /var/lib/openvas/, directory.
chown -R gvm: /var/lib/openvas/su - gvmNext, update the NVTs as openvas user;
greenbone-nvt-syncOnce the update is done, you need to update Redis server with the same VT info from VT files;
sudo openvas --update-vt-infoBuild and Install Greenbone Vulnerability Manager
export PKG_CONFIG_PATH=/opt/gvm/lib/pkgconfig:/opt/heimdal/lib/pkgconfig:$PKG_CONFIG_PATH
cd gvm-source/gvmd
mkdir build && cd build
cmake .. -DCMAKE_INSTALL_PREFIX=/opt/gvm
make
sudo make installBuild and Install Greenbone Security Assistant
export PKG_CONFIG_PATH=/opt/gvm/lib/pkgconfig:/opt/heimdal/lib/pkgconfig:$PKG_CONFIG_PATH
cd ../../gsa
mkdir build && cd build
cmake .. -DCMAKE_INSTALL_PREFIX=/opt/gvm
make
sudo make installExit the gvm user;
exitEnable gvm user to run GSA web application daemon, gsad, with passwordless sudo.
echo "gvm ALL = NOPASSWD: /opt/gvm/sbin/gsad" >> /etc/sudoers.d/gvmKeeping the feeds up-to-date
The gvmd Data, SCAP and CERT Feeds should be kept up-to-date by calling the greenbone-feed-sync script regularly (e.g. via a cron entry):
chown -R gvm: /var/lib/gvmsudo -Hiu gvm greenbone-feed-sync --type GVMD_DATAsudo -Hiu gvm greenbone-feed-sync --type SCAPsudo -Hiu gvm greenbone-feed-sync --type CERTPlease note: The CERT feed sync depends on data provided by the SCAP feed and should be called after syncing the later.
Consider setting cron jobs to run the nvts, cert and scap data update scripts at your preferred frequency to pull updates from the feed servers.
Next, run the command below to generate certificates gvmd. Server certificates are used for authentication while client certificates are primarily used for authorization. More on man gvm-manage-certs.
gvm-manage-certs -achown -R gvm: /opt/gvm/ /var/lib/gvmBuild and Install OSPd and OSPd-OpenVAS
Open Scanner Protocol (OSP) creates a unified interface for different security scanners and makes their control flow and scan results consistently available under the central Greenbone Vulnerability Manager service.
su - gvmexport PKG_CONFIG_PATH=/opt/gvm/lib/pkgconfig:$PKG_CONFIG_PATHBased on the current version of Python installed, set the PYTHONPATH. We use Python 3.7 in this demo.
export PYTHONPATH=/opt/gvm/lib/python3.7/site-packagesmkdir -p /opt/gvm/lib/python3.7/site-packagesBuild OSPD
cd /opt/gvm/gvm-source/ospdpython3.7 setup.py install --prefix=/opt/gvmBuild OSPD-OpenVAS
cd /opt/gvm/gvm-source/ospd-openvaspython3.7 setup.py install --prefix=/opt/gvmRunning OpenVAS Scanner, GSA and GVM services
In order to make the management of OpenVAS scanner, GSA (WebUI service) and GVM daemon, create systemd service unit files for each of them as follows.
Log out as gvm user and execute the commands below as a privileged user.
exitsudo chown -R gvm: /opt/gvm/Creating Systemd Service units for GVM services
Create OSPD OpenVAS systemd service
cat > /etc/systemd/system/ospd-openvas.service << 'EOL'
[Unit]
Description=Description=OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)
After=redis.service
After=postgresql.service
[Service]
ExecStartPre=-rm -rf /run/gvm/ospd-openvas.pid /run/gvm/ospd-openvas.sock
Type=simple
User=gvm
Group=gvm
RuntimeDirectory=gvm
Environment=PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/opt/gvm/bin:/opt/gvm/sbin
Environment=PYTHONPATH=/opt/gvm/lib/python3.7/site-packages
ExecStart=/opt/gvm/bin/ospd-openvas \
--pid-file /run/gvm/ospd-openvas.pid \
--log-file /var/log/gvm/ospd-openvas.log \
--lock-file-dir /run/gvm/ -u /run/gvm/ospd-openvas.sock
RemainAfterExit=yes
[Install]
WantedBy=multi-user.target
EOL
chown -R gvm: /run/gvm /var/log/gvmReload systemd service unit configurations.
systemctl daemon-reloadsystemctl start ospd-openvasCheck the status of the service;
systemctl status ospd-openvas● ospd-openvas.service - Description=OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)
Loaded: loaded (/etc/systemd/system/ospd-openvas.service; enabled; vendor preset: disabled)
Active: active (exited) since Thu 2021-09-30 06:41:59 EAT; 3min 38s ago
Process: 967 ExecStart=/opt/gvm/bin/ospd-openvas --pid-file /run/gvm/ospd-openvas.pid --log-file /var/log/gvm/ospd-openvas.log --lock-file-dir /run/gvm/ -u /run/gvm/ospd>
Process: 965 ExecStartPre=/usr/bin/rm -rf /run/gvm/ospd-openvas.pid /run/gvm/ospd-openvas.sock (code=exited, status=0/SUCCESS)
Main PID: 967 (code=exited, status=0/SUCCESS)
Tasks: 4 (limit: 29841)
Memory: 630.1M
CGroup: /system.slice/ospd-openvas.service
├─1694 /usr/local/bin/python3.7 /opt/gvm/bin/ospd-openvas --pid-file /run/gvm/ospd-openvas.pid --log-file /var/log/gvm/ospd-openvas.log --lock-file-dir /run/gvm>
└─1696 /usr/local/bin/python3.7 /opt/gvm/bin/ospd-openvas --pid-file /run/gvm/ospd-openvas.pid --log-file /var/log/gvm/ospd-openvas.log --lock-file-dir /run/gvm>
Sep 30 06:41:59 rocky8 systemd[1]: Starting Description=OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)...
Sep 30 06:41:59 rocky8 systemd[1]: Started Description=OSPd Wrapper for the OpenVAS Scanner (ospd-openvas).
Check the logs;
tail -f /var/log/gvm/ospd-openvas.logEnable OpenVAS scanner to run on system boot;
systemctl enable ospd-openvasCreate GVMD Systemd Service files
cp /lib/systemd/system/gvmd.service{,.bak}
cat > /lib/systemd/system/gvmd.service << 'EOL'
[Unit]
Description=Greenbone Vulnerability Manager daemon (gvmd)
After=ospd-openvas.service
Wants=postgresql.service ospd-openvas.service
[Service]
Type=simple
User=gvm
Group=gvm
RuntimeDirectory=gvm
Environment=PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/opt/gvm/bin:/opt/gvm/sbin
Environment=PYTHONPATH=/opt/gvm/lib/python3.7/site-packages
ExecStart=/opt/gvm/sbin/gvmd --osp-vt-update=/run/gvm/ospd-openvas.sock --unix-socket=/run/gvm/gvmd.sock
RemainAfterExit=yes
[Install]
WantedBy=multi-user.target
EOL
Reload systemd configs and start GVMD.
systemctl daemon-reloadsystemctl start gvmdCheck the status;
systemctl status gvmd● gvmd.service - Greenbone Vulnerability Manager daemon (gvmd)
Loaded: loaded (/usr/lib/systemd/system/gvmd.service; enabled; vendor preset: disabled)
Active: active (exited) since Thu 2021-09-30 06:41:59 EAT; 6min ago
Process: 968 ExecStart=/opt/gvm/sbin/gvmd --osp-vt-update=/run/gvm/ospd-openvas.sock --unix-socket=/run/gvm/gvmd.sock (code=exited, status=0/SUCCESS)
Main PID: 968 (code=exited, status=0/SUCCESS)
Tasks: 1 (limit: 29841)
Memory: 116.3M
CGroup: /system.slice/gvmd.service
└─1113 gvmd: Waiting for incoming connections
Sep 30 06:41:59 rocky8 systemd[1]: Started Greenbone Vulnerability Manager daemon (gvmd).
Create GSA systemd service Unit file
cp /lib/systemd/system/gsad.service{,.bak}
cat > /etc/systemd/system/gsad.service << 'EOL'
[Unit]
Description=Greenbone Security Assistant daemon (gsad)
Documentation=man:gsad(8) https://www.greenbone.net
After=network.target gvmd.service
Wants=gvmd.service
[Service]
Type=forking
User=gvm
Group=gvm
#PIDFile=/run/gvm/gsad.pid
Environment=PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/opt/gvm/bin:/opt/gvm/sbin:/opt/gvm/.local/bin
Environment=PYTHONPATH=/opt/gvm/lib/python3.7/site-packages
ExecStart=/usr/bin/sudo /opt/gvm/sbin/gsad --munix-socket=/run/gvm/gvmd.sock -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem
RemainAfterExit=yes
[Install]
WantedBy=multi-user.target
Alias=greenbone-security-assistant.service
EOL
Reload system unit configs and start the services;
systemctl daemon-reload
systemctl enable --now gsadChecking the status;
systemctl status gsad● gsad.service - Greenbone Security Assistant daemon (gsad)
Loaded: loaded (/usr/lib/systemd/system/gsad.service; enabled; vendor preset: disabled)
Active: active (exited) since Thu 2021-09-30 06:54:51 EAT; 33s ago
Docs: man:gsad(8)
https://www.greenbone.net
Process: 2242 ExecStart=/usr/bin/sudo /opt/gvm/sbin/gsad --munix-socket=/run/gvm/gvmd.sock -k /var/lib/gvm/private/CA/clientkey.pem -c /var/lib/gvm/CA/clientcert.pem (co>
Sep 30 06:54:51 rocky8 systemd[1]: Starting Greenbone Security Assistant daemon (gsad)...
Sep 30 06:54:51 rocky8 sudo[2242]: gvm : TTY=unknown ; PWD=/ ; USER=root ; COMMAND=/opt/gvm/sbin/gsad --munix-socket=/run/gvm/gvmd.sock -k /var/lib/gvm/private/CA/cli>
Sep 30 06:54:51 rocky8 systemd[1]: Started Greenbone Security Assistant daemon (gsad).
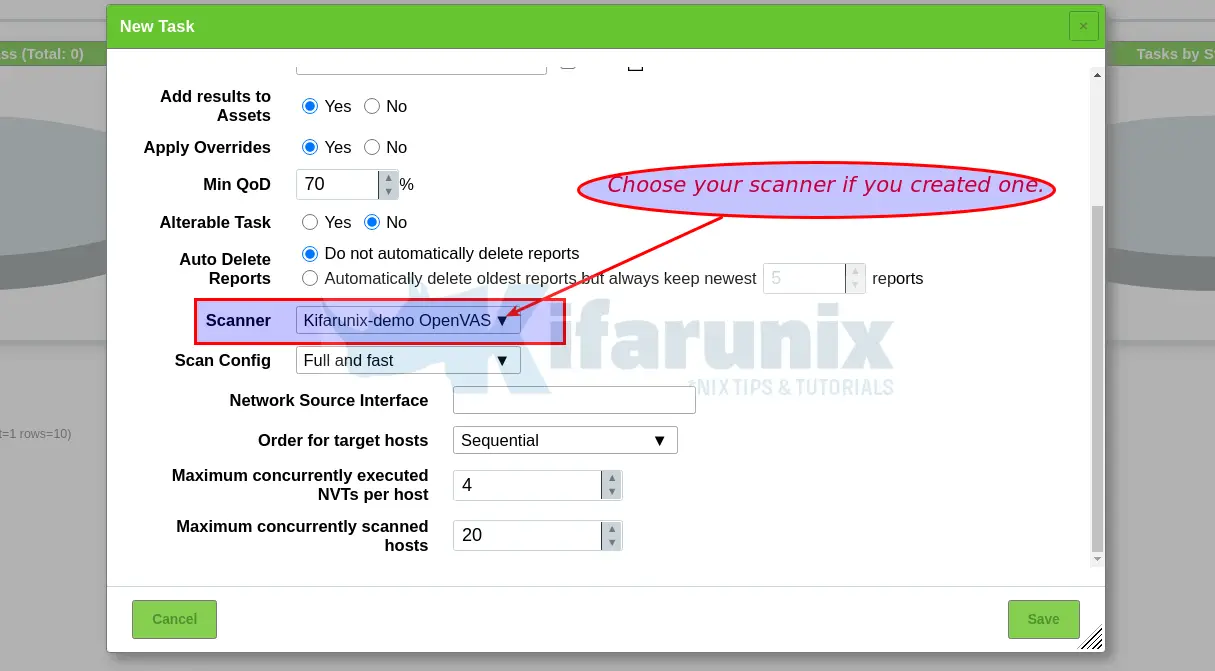
Create GVM Scanner
Since we launched the scanner and set it to use our non-standard scanner host path (/run/gvm/ospd-openvas.sock), we need to create and register our scanner;
sudo -Hiu gvm gvmd --create-scanner="Kifarunix-demo OpenVAS Scanner" --scanner-type="OpenVAS" --scanner-host=/run/gvm/ospd-openvas.sockNext, you need to verify your scanner. For this, you first need to get the scanner identifier;
sudo -Hiu gvm gvmd --get-scanners08b69003-5fc2-4037-a479-93b440211c73 OpenVAS /run/ospd/ospd-openvas.sock 0 OpenVAS Default
6acd0832-df90-11e4-b9d5-28d24461215b CVE 0 CVE
18258727-8815-46ec-b3e6-4d8ce5dcc956 OpenVAS /run/gvm/ospd-openvas.sock 9390 Kifarunix-demo OpenVAS ScannerBased on the output above, our scanner UUID is, 18258727-8815-46ec-b3e6-4d8ce5dcc956.
Verify the scanner;
sudo -Hiu gvm gvmd --verify-scanner=18258727-8815-46ec-b3e6-4d8ce5dcc956Command output;
Scanner version: OpenVAS 21.4.3~dev1~git-e0012eb5-openvas-21.04.Create OpenVAS (GVM) Admin User
Create OpenVAS administrative user by running the command below;
sudo -Hiu gvm gvmd --create-user adminThis command generates a random password for the user. See sample output below;
User created with password 'fee42e66-117c-42f8-9b48-429e51194a13'.If you want to create a user and at the same time create your own password;
sudo -Hiu gvm gvmd --create-user gvmadmin --password=StronGP@SSOtherwise, you can reset the password of an already existing user;
sudo -Hiu gvm gvmd --user=<USERNAME> --new-password=<PASSWORD>An administrator user can later create further users or administrators via clients like the Greenbone Security Assistant (GSA).
Set the Feed Import Owner
According to gvmd/INSTALL.md, certain resources that were previously part of the gvmd source code are now shipped via the feed. An example is the config “Full and Fast”.
gvmd will only create these resources if a “Feed Import Owner” is configured:
sudo -Hiu gvm gvmd --modify-setting 78eceaec-3385-11ea-b237-28d24461215b --value <uuid_of_user>The UUIDs of all created users can be found using
sudo -Hiu gvm gvmd --get-users --verboseSample output;
admin 9a9e5070-d2f0-4802-971e-c9d61e682c21Then modify the gvmd settings with the user UUID.
sudo -Hiu gvm gvmd --modify-setting 78eceaec-3385-11ea-b237-28d24461215b --value 9a9e5070-d2f0-4802-971e-c9d61e682c21GVM Log Files
Various Log files are located under the /opt/gvm/var/log/gvm directory.
ls /opt/gvm/var/log/gvmgsad.logls -1 /var/log/gvm/gvmd.log
openvas.log
ospd-openvas.logAccessing GVM 21.04 (OpenVAS)
Greenbone Security Assistant (GSA) WebUI daemon opens port 443 and listens on all interfaces. If firewall is running, open this port to allow external access.
firewall-cmd --add-port=443/tcp --permanent
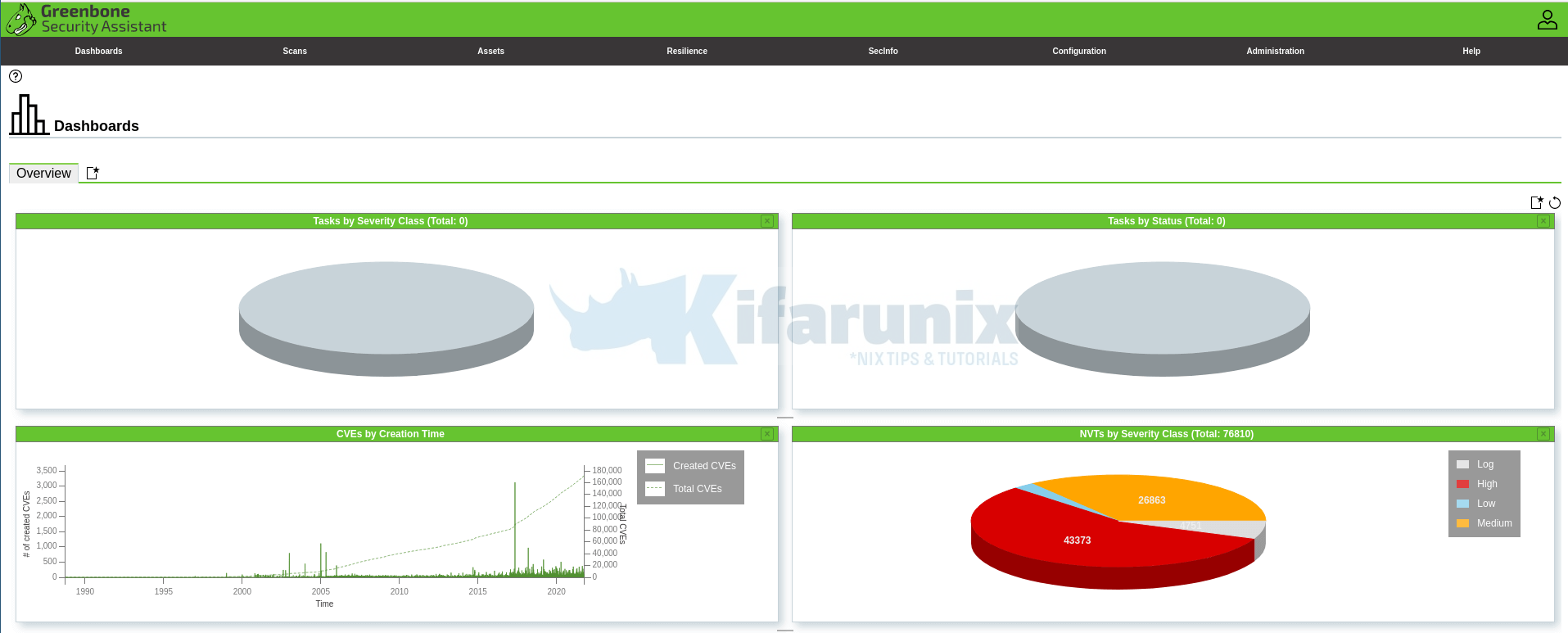
firewall-cmd --reloadYou can now access GSA via the url https:<serverIP-OR-hostname>. Accept the self-signed SSL warning and proceed.
Login with the administrative credentials generated above.
Port lists
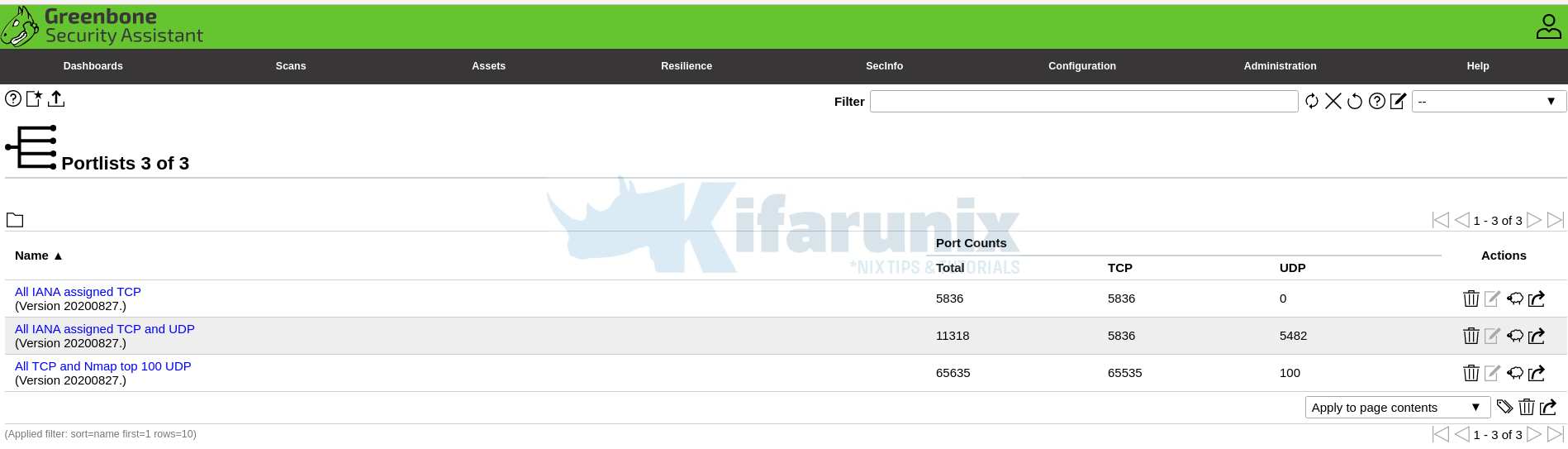
And there you go. That is all it take to install and Setup GVM 21.04 on Rocky Linux 8. You can now start running your scans.
NOTE: When creating a scan task, be sure to select the Scanner we created above.
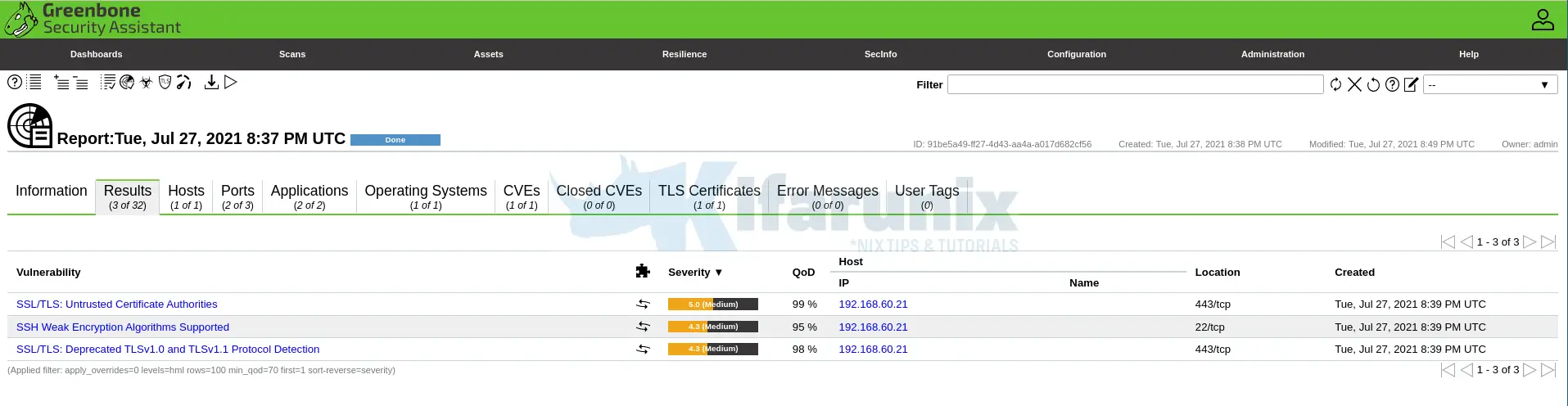
You can now create your target hosts to scan and schedule the scans to run at your own preferred time.
That marks the end of our tutorial on how to install and setup GVM 21.04 on Rocky Linux 8.
Did I miss anything, drop it in the comments section!! Enjoy
Reference
Source files README.md and INSTALL.md files.
Other Tutorials
Install Nikto Web Scanner on Rocky Linux 8


Hi,
I am getting below same error on Centos8 and Ubuntu 20 for OpenVas 20 and 21 –
echo “db_address = /tmp/redis.sock” > /opt/gvm/etc/openvas/openvas.conf
-bash: /opt/gvm/etc/openvas/openvas.conf: No such file or directory
Please help to if I am missing any steps.
-Thanks
Hi Rakesh,
Will have a look at this. But you can use /etc/openvas/openvas.conf instead, in the meantime.
Seems it is updated. Working fine for me. Thanks
Hi.
In the middle of the tutorial you mention a /opt/gvm/var/run/ospd.sock that never existed before. Is this related to /var/run/gvm/ospd-openvas.sock?
Thanks
Ricardo
Seems it is updated actually!
Hey guys, not sure if its only me but whenever i do those git clone commands, the branch isnt found.
bash-4.4$ git clone -b gvm-libs-21.04 https://github.com/greenbone/gvm-libs.git
Cloning into ‘gvm-libs’…
fatal: Remote branch gvm-libs-21.04 not found in upstream origin
bash-4.4$ git clone -b gvm-libs-21.04 https://github.com/greenbone/gvm-libs.git
Cloning into ‘gvm-libs’…
fatal: Remote branch gvm-libs-21.04 not found in upstream origin
bash-4.4$ git clone -b master https://github.com/greenbone/openvas-smb.git
Cloning into ‘openvas-smb’…
fatal: Remote branch master not found in upstream origin
bash-4.4$
Any ideas on this?
Hey Ricardo, our team will update this as soon as possible. In the meantime, please download the source code releases as described here.
Hello
I don’t know if only I have this problem.
When I start cmake .. at gsa, I get the message CMake Error: The source directory “/opt/gvm/gvm-source/gsa” does not appear to contain CMakeLists.txt.
Can you please check this ?
Hi, I am at the step:
cd ../ospd-openvas
python3 setup.py install –prefix=/opt/gvm
The git clone of ospd-openvas does not provide a setup.py.
ospd builds just fine in this way (the prior step).
Is there a prior step in the install that is supposed to create ospd-openvas setup.py?
If not, perhaps the current ospd-openvas has a new build procedure?
I did note, that the previous question posted here comments about CMakeLists.txt missing for gsa. I also came upon this issue. Through the documentation I found that the steps for building gsa where:
yarn
yarn build
Great article. I would certainly like to get it to the finish line. Pretty sure I feed back a ruleset so that SELinux can remain enforced.
Thank you.
I have found that the build for ospd-openvas not longer uses python3 setup.py, it uses poetry. This build process is somewhat documented in the README.md.