This guide will take you through how to install and configure SSSD for LDAP authentication on Ubuntu 20.04. SSSD (System Security Services Daemon) is a system service to access remote directories and authentication mechanisms such as an LDAP directory, an Identity Management (IdM) or Active Directory (AD) domain, or a Kerberos realm.
Configuring SSSD for LDAP Authentication on Ubuntu 20.04
Assuming you already have a running OpenLDAP server, proceed with this guide to learn how to install and configure SSSD for LDAP authentication.
Run System Update
Ensure that your system package cache is up-to-date.
apt updateInstall SSSD on Ubuntu 20.04
To install SSSD and other required SSSD tools on Ubuntu 20.04, run the command below;
apt install sssd libpam-sss libnss-sssConfigure SSSD for OpenLDAP Authentication
Create SSSD configuration file
SSSD do not ship with any configuration file by default. As such, you need to create your configuration file that defines your LDAP authentication specifics.
Below is our sample configuration options;
cat /etc/sssd/sssd.conf
[sssd]
services = nss, pam
config_file_version = 2
domains = default
[nss]
[pam]
offline_credentials_expiration = 60
[domain/default]
ldap_id_use_start_tls = True
cache_credentials = True
ldap_search_base = dc=ldapmaster,dc=kifarunix-demo,dc=com
id_provider = ldap
auth_provider = ldap
chpass_provider = ldap
access_provider = ldap
ldap_uri = ldap://ldapmaster.kifarunix-demo.com
ldap_default_bind_dn = cn=readonly,ou=system,dc=ldapmaster,dc=kifarunix-demo,dc=com
ldap_default_authtok = P@ssWOrd
ldap_tls_reqcert = demand
ldap_tls_cacert = /etc/ssl/certs/ldapcacert.crt
ldap_tls_cacertdir = /etc/ssl/certs
ldap_search_timeout = 50
ldap_network_timeout = 60
ldap_access_order = filter
ldap_access_filter = (objectClass=posixAccount)
Check the highlighted lines above and replace their values appropriately.
For a comprehensive description of options used above, refer to man sssd.conf and man sssd-ldap.
Once you are done with your configurations, save and exit the file.
Install OpenLDAP Server CA Certificate on Ubuntu 20.04 LDAP client
SSSD authentication can only work over an encrypted communication channel. Therefore, your OpenLDAP server must be configured SSL/TLS.
If you have done this already, download the CA certificate from the LDAP server to the LDAP client by executing the command below;
openssl s_client -connect ldapmaster.kifarunix-demo.com:636 -showcerts < /dev/null | openssl x509 -text | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p'if you are downloading the certificates from an OpenLDAP server listening on STARTTLS (port 389/{tcp,udp}), use the command below instead;
openssl s_client -connect ldapmaster.kifarunix-demo.com:389 -starttls ldap -showcerts < /dev/null | openssl x509 -text | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p'Copy the certificate part;
-----BEGIN CERTIFICATE-----
MIIDvzCCAqegAwIBAgIUc8imlOVhEej453dXtvacn7krg1MwDQYJKoZIhvcNAQEL
BQAwbzELMAkGA1UEBhMCS0UxDDAKBgNVBAgMA05haTEMMAoGA1UEBwwDTWFpMRww
GgYDVQQKDBNEZWZhdWx0IENvbXBhbnkgTHRkMSYwJAYDVQQDDB1sZGFwbWFzdGVy
...
...
ExJaMa6cJkIFmepJ6wGvk33DiLRZrAKT2/11yswYm16mdpUynmx6pZvZizjxkq+c
hegnowyEG4db/NktY44v2ryIQdEclnKmhk23vmhgZxl1IUgev2tc//JWPE9dXuP8
Uy7ivNi2PL6mBwxMpyi0zTopqTXSvi54APm48dd0JPsGLTIgPMc1WvaN7TsUeIBs
Igf9K1e9M0Q+j2XEsTeCYVU/v0Jt0kER0+V/NM0IrDOX+6kRz6DNsZrwcMEf5Yvp
ARWZ
-----END CERTIFICATE-----
As per our SSSD configuration, the LDAP CA certificate file is stored as /etc/ssl/certs/ldapcacert.crt on the client. Note that the location of the CA cert file might be different for your case.
Therefore, copy the certificate above and place it in this file;
vim /etc/ssl/certs/ldapcacert.crt-----BEGIN CERTIFICATE-----
MIIDvzCCAqegAwIBAgIUc8imlOVhEej453dXtvacn7krg1MwDQYJKoZIhvcNAQEL
BQAwbzELMAkGA1UEBhMCS0UxDDAKBgNVBAgMA05haTEMMAoGA1UEBwwDTWFpMRww
GgYDVQQKDBNEZWZhdWx0IENvbXBhbnkgTHRkMSYwJAYDVQQDDB1sZGFwbWFzdGVy
...
...
ExJaMa6cJkIFmepJ6wGvk33DiLRZrAKT2/11yswYm16mdpUynmx6pZvZizjxkq+c
hegnowyEG4db/NktY44v2ryIQdEclnKmhk23vmhgZxl1IUgev2tc//JWPE9dXuP8
Uy7ivNi2PL6mBwxMpyi0zTopqTXSvi54APm48dd0JPsGLTIgPMc1WvaN7TsUeIBs
Igf9K1e9M0Q+j2XEsTeCYVU/v0Jt0kER0+V/NM0IrDOX+6kRz6DNsZrwcMEf5Yvp
ARWZ
-----END CERTIFICATE-----
Verify the validity of the certificate;
openssl s_client -connect ldapmaster.kifarunix-demo.com:389 -CAfile /etc/ssl/certs/ldapcacert.crtIf you get, Verification: OK or Verify return code: 0 (ok) on the command output, then you are all set.
Next, open the /etc/ldap/ldap.conf and replace the value of TLS_CACERT with the path to the CA certificate created above.
vim /etc/ldap/ldap.conf...
# TLS certificates (needed for GnuTLS)
#TLS_CACERT /etc/ssl/certs/ca-certificates.crt
TLS_CACERT /etc/ssl/certs/ldapcacert.crtSave and close the configuration file.
Set Proper Permissions on SSSD configurations
After that, assign the root user read/write access to /etc/sssd/.
chmod 600 -R /etc/sssdRestart SSSD service
systemctl restart sssdCheck the status of SSSD to ensure that it is running.
systemctl status sssd● sssd.service - System Security Services Daemon
Loaded: loaded (/lib/systemd/system/sssd.service; enabled; vendor preset: enabled)
Active: active (running) since Fri 2020-05-08 11:38:21 EAT; 6s ago
Main PID: 7004 (sssd)
Tasks: 4 (limit: 2319)
Memory: 34.0M
CGroup: /system.slice/sssd.service
├─7004 /usr/sbin/sssd -i --logger=files
├─7020 /usr/libexec/sssd/sssd_be --domain default --uid 0 --gid 0 --logger=files
├─7021 /usr/libexec/sssd/sssd_nss --uid 0 --gid 0 --logger=files
└─7022 /usr/libexec/sssd/sssd_pam --uid 0 --gid 0 --logger=files
May 08 11:38:20 koromicha systemd[1]: Starting System Security Services Daemon...
May 08 11:38:20 koromicha sssd[7004]: Starting up
May 08 11:38:21 koromicha sssd[be[7020]: Starting up
May 08 11:38:21 koromicha sssd[7021]: Starting up
May 08 11:38:21 koromicha sssd[7022]: Starting up
May 08 11:38:21 koromicha systemd[1]: Started System Security Services Daemon.
Enable SSSD to run on system boot;
systemctl enable sssdConfigure Auto-Home Directory Creation
To enable automatic creation of user’s home directory on first login, you need to configure the PAM modules (pam_mkhomedir.so) as shown below.
Open the /etc/pam.d/common-session configuration file and edit is ad follows;
vim /etc/pam.d/common-sessionAdd the line below just below the line, session optional pam_sss.so.
session required pam_mkhomedir.so skel=/etc/skel/ umask=0022...
# The pam_umask module will set the umask according to the system default in
# /etc/login.defs and user settings, solving the problem of different
# umask settings with different shells, display managers, remote sessions etc.
# See "man pam_umask".
session optional pam_umask.so
# and here are more per-package modules (the "Additional" block)
session required pam_unix.so
session optional pam_sss.so
session required pam_mkhomedir.so skel=/etc/skel/ umask=0022
session optional pam_systemd.so
# end of pam-auth-update config
...
Save and exit the configuration file.
Verify SSSD OpenLDAP authentication
The installation and configuration of SSSD is done. To verify that you can login, try to authenticate against your LDAP server.
In this guide, we have two users, janedoe and johndoe, created on our OpenLDAP Server for demo purposes.
ldapsearch -H ldapi:/// -Y EXTERNAL -b "ou=people,dc=ldapmaster,dc=kifarunix-demo,dc=com" dn -LLL -QThe command above is ran on OpenLDAP server and the output is;
dn: ou=people,dc=ldapmaster,dc=kifarunix-demo,dc=com
dn: uid=janedoe,ou=people,dc=ldapmaster,dc=kifarunix-demo,dc=com
dn: uid=johndoe,ou=people,dc=ldapmaster,dc=kifarunix-demo,dc=comOn the Ubuntu 20.04 ldap client, these information about the users above should now be printable.
root@ubuntu20:~# id johndoeuid=10000(johndoe) gid=10000(johndoe) groups=10000(johndoe)root@ubuntu20:~# id janedoeuid=10010(janedoe) gid=10010(janedoe) groups=10010(janedoe)To demo the SSSD LDAP authentication, we will use both SSH and GUI based authentication;
Verify SSH Authentication via OpenLDAP SSSD
ssh johndoe@ubuntu20
The authenticity of host 'ubuntu20 (192.168.58.19)' can't be established.
ECDSA key fingerprint is SHA256:gN94vPFvyZ3Rdeb/+7R+0QJy9S4MdWmgJyEShIG9YgE.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added 'ubuntu20' (ECDSA) to the list of known hosts.
johndoe@ubuntu20's password:
Creating directory '/home/johndoe'.
Welcome to Ubuntu 20.04 LTS (GNU/Linux 5.4.0-29-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
* Ubuntu 20.04 LTS is out, raising the bar on performance, security,
and optimisation for Intel, AMD, Nvidia, ARM64 and Z15 as well as
AWS, Azure and Google Cloud.
https://ubuntu.com/blog/ubuntu-20-04-lts-arrives
13 updates can be installed immediately.
9 of these updates are security updates.
To see these additional updates run: apt list --upgradable
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
johndoe@ubuntu20:~$
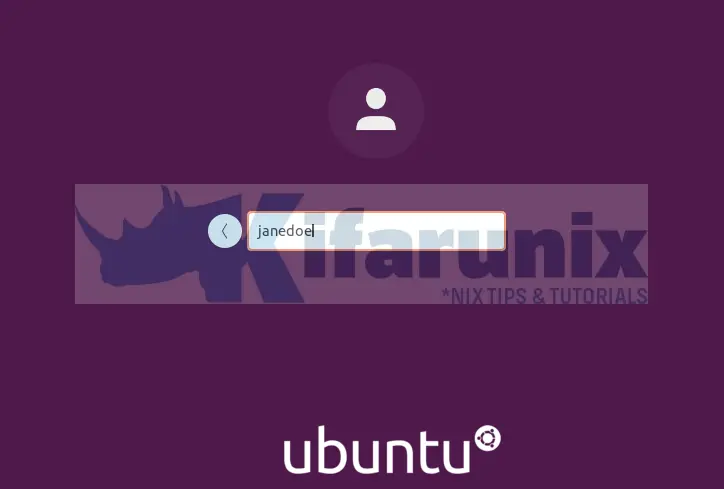
Verify GUI authentication via OpenLDAP SSSD
Reboot your Ubuntu 20.04 desktop after SSSD setup and and verify authentication.
Once it boots, on the GDM login interface, click Not listed to enter your OpenLDAP username and password.
We logged in on GUI as a different LDAP user, janedoe.
Upon successful login, you land on Ubuntu 20.04 desktop.
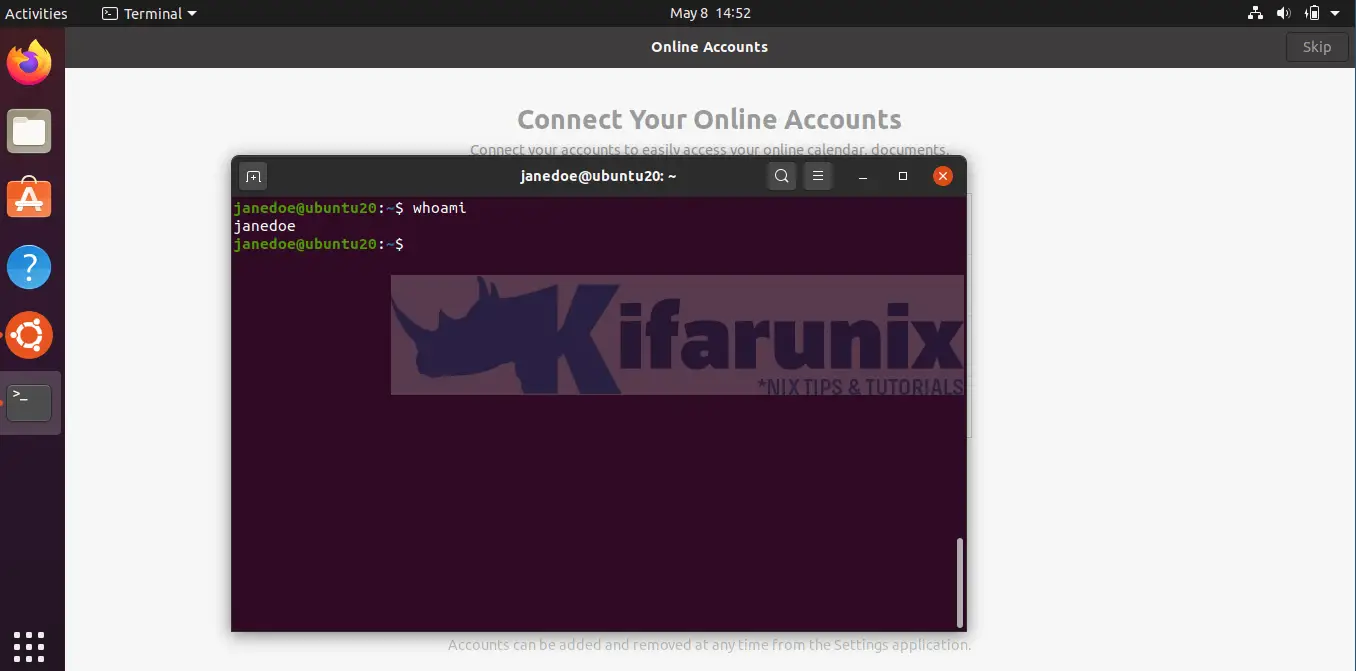
And there you go. You have successfully installed and configured SSSD for LDAP Authentication on Ubuntu 20.04.
Related Tutorials
Configure SSSD for OpenLDAP Authentication on Ubuntu 18.04
Install phpLDAPadmin on CentOS 8
Configure ownCloud OpenLDAP Authentication


what do you mean by the LDAP CA certificate file is stored as etc/ssl/certs/cacert.crt? I open the folder it is empty (both ther server and client).
And is there any typo in your command here “openssl s_client -connect ldapmaster.kifarunix-demo.com:389 -CAfile /etc/ssl/certs/cacert.crt”? Because i cannot find cacert.crt folder at the directory (both server and client). It is supposed to be /etc/ssl/openldap/certs/cacert.pem? because there is where the CA file is stored at the server. Am i right?
Well that depends from the point you are looking this from. You can choose to store the certs in any of your preferred directories.
As per our SSSD configuration, that is the location where we put our CA cert file.
So basically, “openssl s_client -connect ldapmaster.kifarunix-demo.com:389 -CAfile /etc/ssl/certs/cacert.crt” command is we supposed to put the directories at the server or directories that we want to put at the client?
for “As per our SSSD configuration”, by you mean location is at the server or at the client?
Im confused. Because all the configuration from the server directories until the client directories, Im copied from yours. But I cannot pass untill the Verification: OK or Verify return code: 0 (ok). Please enlighten me. Thanks
Basically, on the LDAP client system where you installed SSSD, you need to install the CA certificate that you configured your LDAP server to use.
In this setup, the certificate file should be ldapcacert.crt and not cacert.crt, as previously shown, and is stored under /etc/ssl/certs/ directory on a client system.
Hi! im getting “this account is currently not available.”
you have any clue?
Thanks in advance
Running the command below:
ldapsearch -H ldapi://rufus.ayarlabs.com -Y EXTERNAL -b “” dn -LLL -Q
results in the error:
ldap_sasl_interactive_bind_s: Can’t contact LDAP server (-1)
Any suggestions on where to look to fix it. I think it would be useful to run these searches from the clients.
Hi Andy,
Well, you can try ldapsearch with simple authentication from your client.
ldapsearch -x -h rufus.ayarlabs.com -W -D "root bind DN" -b "" dn -LLLWhere,
root bind DNcan be sth like,cn=Manager,dc=rufus,dc=ayarlabs,dc=comcheck
man ldapsearch.I can get as far as editing the pam files, but the ldapsearch command doesn’t work, nor does the id command. They both work fine from the openldap server itself, though.
Please advise
Hi Larry,
It sounds like you cant connect to LDAP server from the client?
Telnet to the ports (389/636) work?
I am able to use the following to get it to work:
ldapsearch -x -h auth.wapnet.local.lan -W -D “cn=admin,dc=wapnet,dc=local,dc=lan” -b “dc=wapnet,dc=local,dc=lan” dn -LLL
telnet to 389 works
Verify the user using the command;
ldapwhoami -h auth.wapnet.local.lan -x -D "cn=user,dc=wapnet,dc=local,dc=lan" -Wkoromicha.. I went through all 3 of your tutorials, and I can’t seem to get it to work right.. At one point in time I had at least “id” working, but currently thats not working. the best scenario I had I couldn’t get ssh to work, it would immediately.. I’ve been reimaging a VPS over & over again… Currently I have a gist up of my setup script which is basically a scripted version of your the 3 tutorials (this one, sssd, and ssl generation).. Maybe you can identify what I’m missing?
https://gist.github.com/itsnotyoutoday/f20a5450ab32cd8d10769dd9d066fa51
Thanks
Hi Rick, let me have a look at this and update you as soon as i can
I found a couple errors in my script.. Mostly it wasn’t taking the ldap sudo code, and so on.. I redid that by using sed’s on the sudo schema and importing it… However, its still not working… Maybe it helps to know I’m configuring a sub.domain.com as the ldap server, not just a domain.com (hence why I’m forcing settings into the ldap install.. Otherwise have to use dpkg-reconfigure to get it to take). I have this script setup to be the first thing I’m doing on a Ubuntu 20.04 VPS, and its currently running with absolutely zero errors; save for no LDAP user authentication happening for id or ssh.
~# ldapsearch -H ldapi:/// -Y EXTERNAL -b “ou=members,o=company” dn -LLL -Q
result:
ldap_sasl_interactive_bind_s: Can’t contact LDAP server (-1)
Hi, from where are you running the command? LDAP client?
Thank you very much! This was very helpful for setting up ldap-authentication.