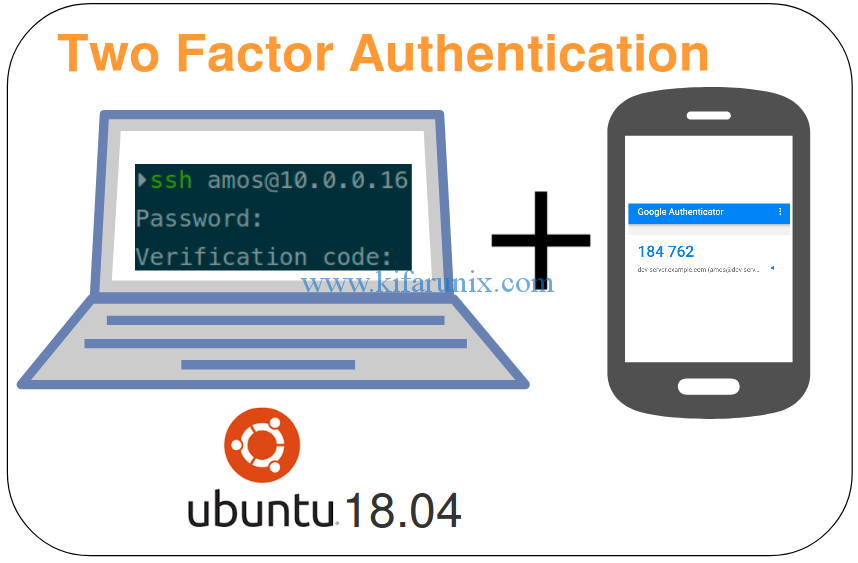
Welcome to our guide on how to enable SSH 2-Factor authentication on Ubuntu 18.04 system.
Under normal circumstances, we usually login to a remote system with SSH using either a normal username and password combination or a public key. In order to add another layer of security such that you need to verify who you tell the system you are, you need to configure two-factor authentication (2FA), a subset of multi-factor authentication. In this guide, we are going to use Google Authenticator on Ubuntu 18.04 to enable the 2FA. Without much theory, let’s get to it.
Enable SSH 2-Factor Authentication on Ubuntu 18.04
To enable SSH 2FA on Ubuntu 18.04 system, proceed as follows;
Install Google Authenticator PAM
Google Authenticator is a Pluggable Authentication Module for Linux systems that generates Time-based One-Time Password (TOTP) used for authentication. This module is available on the default Ubuntu repositories and can be simply installed by running the command below;
apt install libpam-google-authenticator
Generate the TOTP for users
To enable 2FA for a user, you need generate the TOTP for each one of them that you need to enable 2FA for by running the command;
google-authenticator
The google-authenticator command will prompt for some information required to enable 2FA for a user.
The first prompt will ask you to choose whether to generate time-based authentication tokens. There are two types of authentication tokens for Google authenticator PAM; sequential-based tokens and time-based tokens. While sequential-based tokens provides a code that increments from a specific after every use, time-based tokens will keep changing randomly every time. Hence, type y and press Enter to generate time-based tokens.
Do you want authentication tokens to be time-based (y/n) y
This generates a large QR code along with the secret key, the verification code and emergency recovery codes.
Proceed to configure Google Authenticator by updating the configuration file, .google_authenticator.
Do you want me to update your "/home/amos/.google_authenticator" file? (y/n) y
Disable multiple uses of the same authentication token to prevent MITMA
Do you want to disallow multiple uses of the same authentication token? This restricts you to one login about every 30s, but it increases your chances to notice or even prevent man-in-the-middle attacks (y/n) y
Set the token to expire immediately after use to prevent replay attacks.
By default, a new token is generated every 30 seconds by the mobile app. In order to compensate for possible time-skew between the client and the server, we allow an extra token before and after the current time. This allows for a time skew of up to 30 seconds between authentication server and client. If you experience problems with poor time synchronization, you can increase the window from its default size of 3 permitted codes (one previous code, the current code, the next code) to 17 permitted codes (the 8 previous codes, the current code, and the 8 next codes). This will permit for a time skew of up to 4 minutes between client and server. Do you want to do so? (y/n) y
Enable rate-limiting to prevent brute-force attacks. This allows a certain number of login attempts after which you are blocked.
If the computer that you are logging into isn't hardened against brute-force login attempts, you can enable rate-limiting for the authentication module. By default, this limits attackers to no more than 3 login attempts every 30s. Do you want to enable rate-limiting? (y/n) y
To backup your secret, copy the .google_authenticatoe file and save it somewhere safe.
Enable SSH 2FA on Ubuntu 18.04
To enable SSH 2FA, you need to configure SSH as follows;
Edit the /etc/pam.d/sshd and add the line, auth required pam_google_authenticator.so, at the end of the file.
vim /etc/pam.d/sshd
auth required pam_google_authenticator.so
If you need to make 2FA optional such that those who don’t have the TOTP token can login with their password or SSH key, you can add the keyword nullok on the same line as in;
auth required pam_google_authenticator.so nullokEnable challenge-response passwords on SSH by editing the SSH configuration file and setting the value of ChallengeResponseAuthentication no to yes.
vim /etc/ssh/sshd_config
ChallengeResponseAuthentication yes
Restart the SSH daemon
systemctl restart sshd
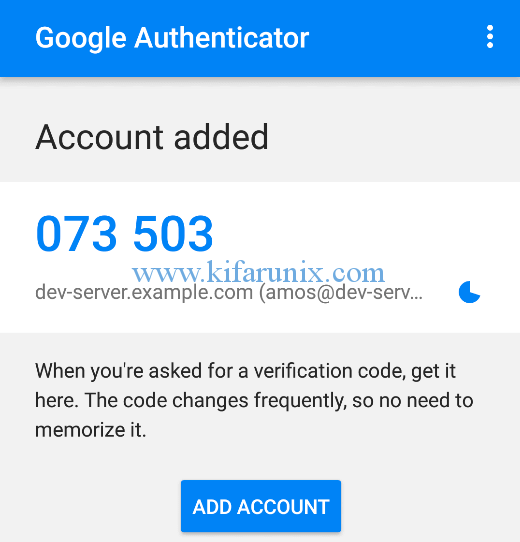
Assuming you have already install the Google Authenticator App on your phone, you need to add the secret key generated to make it work. To simplify this, open the generated QR code link on the browser to access a sizeable QR code.
- Open your Google-authenticator APP and click BEGIN button.
- Click Scan a barcode to scan the barcode on your browser.
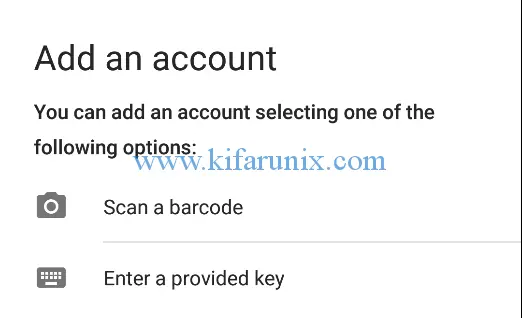
- Click ADD ACCOUNT to add your account.
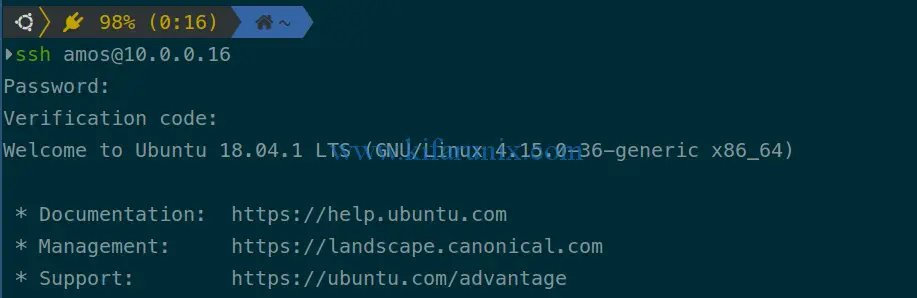
There you go, open a new ssh session and login as the user whose 2FA is enabled.
Congratulations. You have successfully gone through all the steps required to enable SSH 2-Factor Authentication on Ubuntu 18.04. Enjoy.