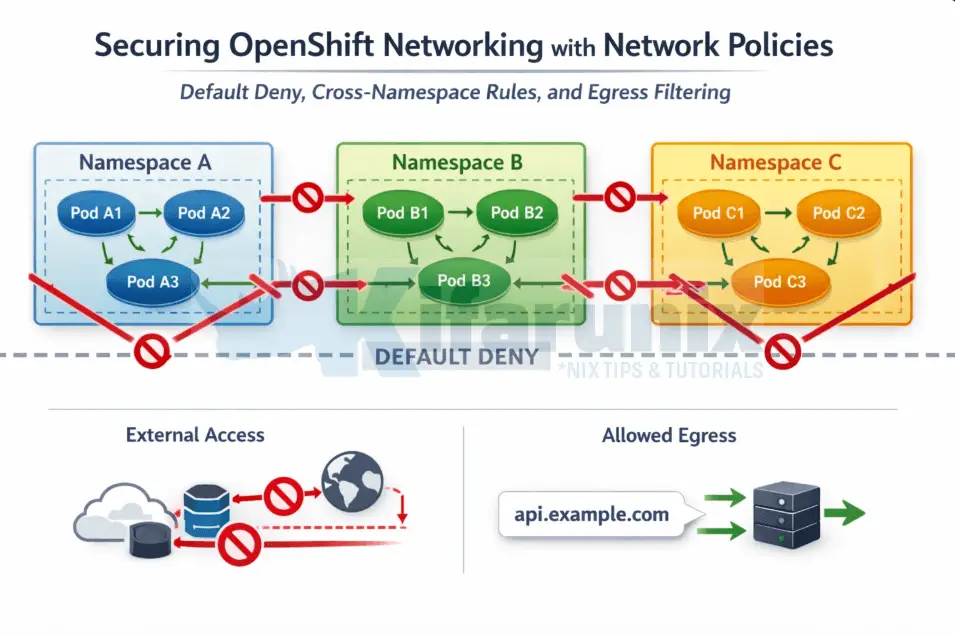
Securing OpenShift Networking with Network Policies: Default Deny, Cross-Namespace Rules, and Egress Filtering
Securing OpenShift networking with network policies is one of the most critical steps in moving from a flat, permissive cluster to a production-ready, zero-trust architecture.