With the pandemic relegating much of the knowledge workforce to the home office, it comes as no surprise that cyber threats targeting home and small office users are at an all-time high. Phishing emails have increased by over 600% since February 2021 as malicious actors look to capitalize on the disarray caused by the global crisis.
As the line between home and workplace continues to blur, businesses and consumers face a new set of cyber risk challenges in adjusting to the new office normal.
Do You Need a Personal Firewall?
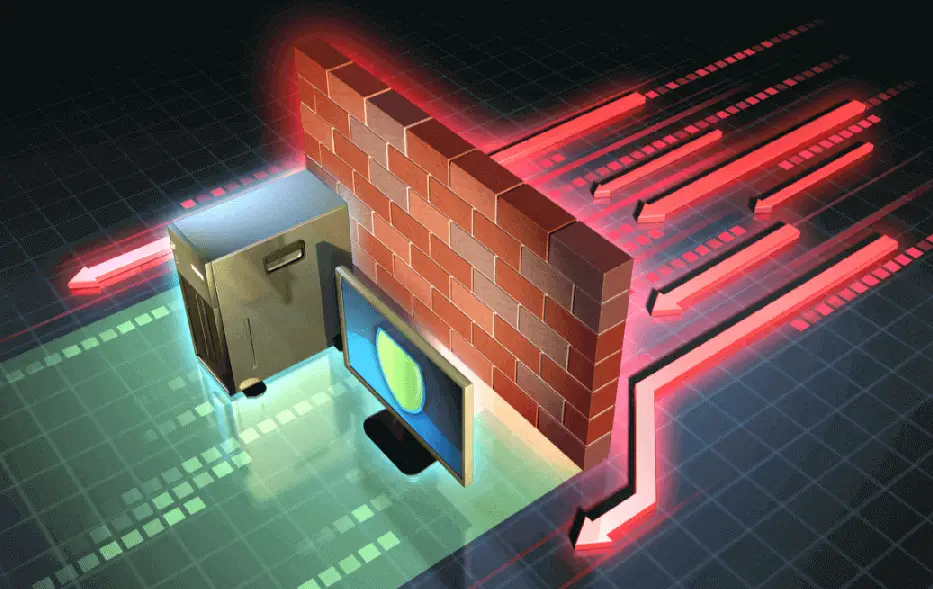
In a business IT environment, a network firewall shields the organization’s internal network from external internet traffic. Because traffic flowing back and forth first traverses this specialized network device, the firewall is effectively the first line of defense for internal users against outside cyberattackers.
A personal firewall is no different. Operating on the same principal, it enables safe communication to occur from the internal network to the outside world and vice versa. Without it, home network users are directly exposed and could become a victim of an attack happening every 39 seconds.
Understanding Firewalls for Home and Small Office
Firewalls work by filtering out unwanted traffic based on a set of rules, which may specify restrictions per protocol, port number, IP address, or other criteria. In a home or small office environment, this typically happens at the hardware firewall, with a software firewall deployed for additional security.
As the main gateway to the internet, the ISP-provided router or modem usually functions as the hardware firewall. On the desktop (e.g., Windows Defender for Windows), a software firewall offers more granular security at the application level. The use of a hardware firewall in conjunction with a software firewall provides the necessary layered security for surviving today’s cyber threat landscape.
How Important Is a Firewall and Who Needs One?
The hardware firewall is without a doubt the most critical security device in the home and small office environment. Without it, all computers on the user’s personal network would be directly exposed to the wilds of the internet. For this reason, ISPs typically bundle the hardware firewall or router as part of the customer’s installation package. This allows for a plug-and-play experience for the end-user, security to boot.
Similarly, popular operating systems like Windows come with a software firewall installed for providing local security to the host computer. These applications will typically monitor the computer for suspicious behavior and block traffic or access if anomalies are detected. Other operating systems such as the macOS do not ship with any sort of software firewall installed by default. In these cases, a myriad of third-party options can be purchased and installed separately.
Is the Firewall Just a Box?
In the case of a software firewall, the operative security mechanism is an application installed on the host computer directly. In contrast, a hardware firewall is a metal box with specialized networking components. However, the software installed on it is also key to its operations.
The following are five types of firewalls categorized by their operative security mechanism and structure:
Packet Filtering Firewall
The most rudimentary firewall mechanism on the list, packet filtering involves running a simple check of the data going through the device. If the traffic doesn’t meet specific criteria, the packets are dropped.
Circuit-Level Gateway
Circuit-level gateways employ a fairly basic approve/deny security model based on the verification of the User Datagram Protocol (UDP) and Transmission Control Protocol (TCP) handshake. It’s worth noting that this security mechanism only provides assurances that the packet’s session is legitimate. It does not analyze the contents of the packet itself.
Application-Level Gateway
Also known as proxy firewalls, application-level gateways act as an intermediary between the internal network and the internet—in this case, by acting on behalf of the network’s application servers. When a request occurs, the application acts as a proxy to prevent direct access to the destination system.
Stateful Inspection Firewall
Stateful inspection combines both packet filtering and TCP handshake verification for more sophisticated protection against external threats. Subsequently, these types of firewalls consume significantly more computing and memory resources.
Next-Generation Firewall (NGFW)
Though no strict industry definition exists for the next-generation firewall (NGFW), most firewall vendors tend to assemble the same set of features in their NGFW offerings: deep packet inspection (DPI), built-in intrusion detection and prevention system (IDPS), artificial intelligence/machine learning (AI/ML)-based anomaly detection, third-party threat intelligence feeds, and more. These firewall devices were designed in response to the evolving sophistication of cyber threats and the growing need for advanced protection.
Why Do Enterprises Choose TAA Firewalls for Their Organization?
Enacted in 1979 by the U.S. Congress, the Trade Agreements Act (TAA) requires all parties bidding for a government contract to certify that their end products are in compliance—specifically, that they were manufactured or substantially transformed in the US or TAA-listed country.
Some enterprises may only select TAA firewalls to ensure that implicit high standards are met. Others may be required to do so due to their involvement in U.S. government projects.
To validate that products, components, sourced parts, and subparts meet TAA certification requirements for U.S. government procurement, enterprises must prove one of the following:
- That they are manufactured in the US or TAA-compliant country
- That they are substantially transformed into an end product in the US or TAA-compliant country
The end goal of the TAA is to create harmonization, fairness, and transparency in the trade and global marketplace—with the result being safer, higher-caliber products. This alone is enough of an incentive for many enterprises to select TAA firewalls. In selecting a network firewall, enterprises may look to the vendor’s website to verify if their products are in compliance with TAA regulations.
For example:
- SonicWall offers TAA compliance assurances on its federal government cybersecurity page.
- Fortinet compliance and related information can be found on the Fortinet TAA page.
- Barracuda Networks has a federal government compliance page that also lists some of its government customers.
Strong cybersecurity starts with a competent firewall box—but it doesn’t stop there. Endpoint protection, IDPS, and antivirus (AV) are also critical for protecting the home and small office from malicious actors both inside and outside the network. Also, employing both a software and hardware firewall provides another layer of protection against cyberattacks.